FF65 is scheduled for release 29th Jan
FF65 release notes [when ready]
[FF65 for developers](https://developer.mozilla.org/en-US/docs/Mozilla/Firefox/Releases/65)
FF65 compatibility
FF65 security advisories
154 diffs ( 84 new, 45 gone, 25 different )
other
- [x]
2516disable PointerEvents -> RFP ALT - https://github.com/ghacksuserjs/ghacks-user.js/commit/ec0e58099f0669683d109b1d847fe73db18a450e
new in v65.0:
- [x] pref("browser.discovery.enabled", true); - 1499470 - https://github.com/ghacksuserjs/ghacks-user.js/commit/f1b892bc1c8cacdbfc1a32ba87ad1a241a52e922
- [x] pref("dom.storage_access.enabled", true); - MDN - https://github.com/ghacksuserjs/ghacks-user.js/commit/24f2e1d9829212077cbc5a4df92b877fcbfde8ea - https://github.com/ghacksuserjs/ghacks-user.js/commit/e6eb4730719bca426c73595cf5e07646baa543fa
- :hatching_chick: just to be clear, I WAS (see below) only disabling this because it is ABUSING the permissions.sqlite, and it is a new API that no other browser has yet (except experimental Safari). Otherwise, you already have mechanisms to control 3rd parties, JS, storage, etc. The actual API itself is fine, solves issues with breakage (read the MDN link) and is a request on a site by site basis. This pref has been added to the watchlist sticky to revisit when they stop ABUSING permissions.sqlite
- :hatched_chick: update: this pref has no affect on the permissions.sqlite file being abused, so it will not be disabled
- [x] pref("dom.targetBlankNoOpener.enabled", false); - 1503681 - to be enabled by default in FF67 - https://github.com/ghacksuserjs/ghacks-user.js/commit/3847f97f4166f2a5f5080d13c92165e702ae9a22
- [x] pref("network.connectivity-service.enabled", true); - https://github.com/ghacksuserjs/ghacks-user.js/commit/649699ad22123bf5ae88e1b57d3a552e69946c6c
- [x] pref("network.http.spdy.websockets", true); 1434137 - https://github.com/ghacksuserjs/ghacks-user.js/commit/2f351fa5ce23edeed569b7ad7004cd9ac0afc382
- FYI
- pref("browser.security.newcerterrorpage.mitm.enabled", false); - 1450784
- pref("dom.block_multiple_popups", true); - 675574, Compat
- pref("dom.reporting.enabled", false); - 1492036 - w3c
- pref("network.trr.custom_uri", ""); - added to the watchlist sticky to maybe get addressed down the track
- MDN Feature-Policy header
- FF63+: dom.security.featurePolicy.enabled (still default false)
- FF65+: pref("dom.security.featurePolicy.header.enabled", false);
- FF65+: pref("dom.security.featurePolicy.webidl.enabled", false);
- pref("security.strict_security_checks.enabled", false); - 1498526 - needs testing
removed, renamed or hidden in v65.0:
DONE - https://github.com/ghacksuserjs/ghacks-user.js/commit/d9a87b3ac4b7b794ff4fad7a9d1aed4a704566af
- [x] FYI: pref("app.update.auto", true); - only removed in Windows, the UI setting still works
- [x] pref("browser.contentblocking.enabled", true); - 1501978
- removed from the user.js: it was added in FF63 and was default true anyway
- [x] pref("browser.fixup.hide_user_pass", true); - 1510580
- [x] pref("browser.urlbar.autocomplete.enabled", true); - 1502392
- https://support.mozilla.org/en-US/questions/1248199#answer-1192146 - if you want to stop the dropdown you can use CSS
- still used in Android
changed in v65.0:
- [x] pref("geo.provider.ms-windows-location", true); // prev: false - 1512161 - https://github.com/ghacksuserjs/ghacks-user.js/commit/3847f97f4166f2a5f5080d13c92165e702ae9a22
- pref("browser.newtabpage.activity-stream.asrouter.providers.snippets", "{\"id\":\"snippets\",\"enabled\":true,\"type\":\"remote\",\"url\":\"https://snippets.cdn.mozilla.net/%STARTPAGE_VERSION%/%NAME%/%VERSION%/%APPBUILDID%/%BUILD_TARGET%/%LOCALE%/%CHANNEL%/%OS_VERSION%/%DISTRIBUTION%/%DISTRIBUTION_VERSION%/\",\"updateCycleInMs\":14400000}"); // prev: "{\"id\":\"snippets\",\"enabled\":false,\"type\":\"remote\",\"url\":\"https://snippets.cdn.mozilla.net/%STARTPAGE_VERSION%/%NAME%/%VERSION%/%APPBUILDID%/%BUILD_TARGET%/%LOCALE%/%CHANNEL%/%OS_VERSION%/%DISTRIBUTION%/%DISTRIBUTION_VERSION%/\",\"updateCycleInMs\":14400000}" -
0105b
ignore
==NEW ==REMOVED or HIDDEN ==CHANGEDclick me for details
pref("apz.relative-update.enabled", true);
pref("browser.contentblocking.control-center.ui.showAllowedLabels", false);
pref("browser.contentblocking.control-center.ui.showBlockedLabels", true);
pref("browser.discovery.containers.enabled", true);
pref("browser.discovery.sites", "addons.mozilla.org");
pref("browser.engagement.recent_visited_origins.expiry", 86400);
pref("browser.sessionstore.warnOnQuit", false);
pref("devtools.aboutdebugging.network", false);
pref("devtools.aboutdebugging.wifi", false);
pref("devtools.console.stdout.chrome", false);
pref("devtools.console.stdout.content", false);
pref("devtools.debugger.end-panel-size", 300);
pref("devtools.debugger.features.origial-blackbox", false);
pref("devtools.debugger.features.xhr-breakpoints", true);
pref("devtools.debugger.logging", false);
pref("devtools.debugger.start-panel-size", 300);
pref("devtools.debugger.xhr-breakpoints-visible", true);
pref("devtools.inspector.showUserAgentShadowRoots", false);
pref("devtools.performance.profiler.sample-frequency-hz", 1000);
pref("devtools.recordreplay.allowRepaintFailures", true);
pref("devtools.recordreplay.includeSystemScripts", false);
pref("devtools.recordreplay.timeline.enabled", false);
pref("dom.compositionevent.text.dispatch_only_system_group_in_content", true);
pref("dom.ipc.tabs.createKillHardCrashReports", false);
pref("dom.keyboardevent.keypress.hack.dispatch_non_printable_keys", "");
pref("dom.keyboardevent.keypress.hack.use_legacy_keycode_and_charcode", "");
pref("dom.payments.request.supportedRegions", "US,CA");
pref("dom.performance.time_to_contentful_paint.enabled", false);
pref("dom.reporting.cleanup.timeout", 3600);
pref("dom.reporting.delivering.maxFailures", 3);
pref("dom.reporting.delivering.maxReports", 100);
pref("dom.reporting.delivering.timeout", 5);
pref("dom.reporting.featurePolicy.enabled", false);
pref("dom.reporting.header.enabled", false);
pref("dom.reporting.testing.enabled", false);
pref("dom.sidebar.enabled", true);
pref("dom.storage.next_gen", false);
pref("dom.storage.shadow_writes", true);
pref("dom.storage.snapshot_prefill", 16384);
pref("dom.storage.snapshot_reusing", true);
pref("dom.storage_access.auto_grants", true);
pref("dom.storage_access.max_concurrent_auto_grants", 5);
pref("extensions.formautofill.reauth.enabled", false);
pref("gfx.omta.background-color", false);
pref("gfx.webrender.dcomp-win-triple-buffering.enabled", true);
pref("gfx.webrender.debug.slow-frame-indicator", false);
pref("gfx.webrender.debug.texture-cache.clear-evicted", true);
pref("gfx.webrender.picture-caching", false);
pref("image.animated.decode-on-demand.recycle", true);
pref("image.webp.enabled", true);
pref("javascript.options.bigint", false);
pref("layout.css.step-position-jump.enabled", true);
pref("media.av1.use-dav1d", false);
pref("media.getusermedia.use_aec_mobile", false);
pref("media.navigator.mediadatadecoder_vpx_enabled", false);
pref("media.rdd-process.enabled", true);
pref("media.rdd-process.startup_timeout_ms", 5000);
pref("media.test.video-suspend", false);
pref("network.connectivity-service.DNSv4.domain", "mozilla.org");
pref("network.connectivity-service.DNSv6.domain", "mozilla.org");
pref("network.connectivity-service.IPv4.url", "http://detectportal.firefox.com/success.txt?ipv4");
pref("network.connectivity-service.IPv6.url", "http://detectportal.firefox.com/success.txt?ipv6");
pref("network.http.spdy.enable-hpack-dump", false);
pref("network.IDN.extra_allowed_chars", "");
pref("network.IDN.extra_blocked_chars", "");
pref("privacy.popups.maxReported", 100);
pref("privacy.restrict3rdpartystorage.partitionedHosts", "accounts.google.com/o/oauth2/");
pref("privacy.restrict3rdpartystorage.userInteractionRequiredForHosts", "");
pref("services.sync.prefs.sync.privacy.fuzzyfox.clockgrainus", false);
pref("services.sync.prefs.sync.privacy.fuzzyfox.enabled", false);
pref("toolkit.tabbox.switchByScrolling", false);
pref("urlclassifier.trackingAnnotationSkipURLs", "google.com/recaptcha/,*.google.com/recaptcha/");
pref("browser.contentblocking.cookies-site-data.ui.reject-trackers.enabled", true);
pref("browser.contentblocking.cookies-site-data.ui.reject-trackers.recommended", true);
pref("browser.contentblocking.fastblock.control-center.ui.enabled", false);
pref("browser.contentblocking.fastblock.ui.enabled", false);
pref("browser.contentblocking.global-toggle.enabled", false);
pref("browser.contentblocking.rejecttrackers.ui.enabled", true);
pref("browser.contentblocking.rejecttrackers.ui.recommended", true);
pref("browser.contentblocking.trackingprotection.ui.enabled", true);
pref("browser.contentblocking.ui.enabled", true);
pref("browser.fastblock.enabled", false);
pref("browser.fastblock.limit", 20000);
pref("browser.fastblock.timeout", 5000);
pref("browser.schedulePressure.defaultCount", 3);
pref("browser.schedulePressure.enabled", true);
pref("browser.schedulePressure.timeoutMs", 300);
pref("browser.tabs.20FpsThrobber", false);
pref("browser.tabs.30FpsThrobber", false);
pref("browser.urlbar.matchBehavior", 1);
pref("browser.urlbar.suggest.history.onlyTyped", false);
pref("canvas.customfocusring.enabled", false);
pref("canvas.imagebitmap_extensions.enabled", false);
pref("devtools.debugger.features.event-listeners", false);
pref("devtools.debugger.forbid-certified-apps", true);
pref("devtools.debugger.new-debugger-frontend", true);
pref("devtools.inspector.fonteditor.enabled", true);
pref("devtools.performance.profiler.sample-frequency-khz", 1);
pref("dom.browserElement.maxScreenshotDelayMS", 2000);
pref("dom.webcomponents.customelements.enabled", true);
pref("dom.webcomponents.shadowdom.enabled", true);
pref("io.activity.intervalMilliseconds", 0);
pref("layout.css.frames-timing.enabled", false);
pref("layout.css.overflow-break.intrinsic-size", false);
pref("layout.css.shape-outside.enabled", true);
pref("layout.css.text-align-unsafe-value.enabled", false);
pref("media.navigator.mediadatadecoder_enabled", false);
pref("network.IDN.blacklist_chars", "\u0020\u00A0\u00BC\u00BD\u00BE\u01C3\u02D0\u0337\u0338\u0589\u058A\u05C3\u05F4\u0609\u060A\u066A\u06D4\u0701\u0702\u0703\u0704\u115F\u1160\u1735\u2000\u2001\u2002\u2003\u2004\u2005\u2006\u2007\u2008\u2009\u200A\u200B\u200E\u200F\u2010\u2019\u2024\u2027\u2028\u2029\u202A\u202B\u202C\u202D\u202E\u202F\u2039\u203A\u2041\u2044\u2052\u205F\u2153\u2154\u2155\u2156\u2157\u2158\u2159\u215A\u215B\u215C\u215D\u215E\u215F\u2215\u2236\u23AE\u2571\u29F6\u29F8\u2AFB\u2AFD\u2FF0\u2FF1\u2FF2\u2FF3\u2FF4\u2FF5\u2FF6\u2FF7\u2FF8\u2FF9\u2FFA\u2FFB\u3000\u3002\u3014\u3015\u3033\u30A0\u3164\u321D\u321E\u33AE\u33AF\u33C6\u33DF\uA789\uFE14\uFE15\uFE3F\uFE5D\uFE5E\uFEFF\uFF0E\uFF0F\uFF61\uFFA0\uFFF9\uFFFA\uFFFB\uFFFC\uFFFD");
pref("pdfium.enabled", false);
pref("privacy.trackingprotection.introCount", 0);
pref("services.sync.prefs.sync.browser.contentblocking.enabled", true);
pref("services.sync.prefs.sync.browser.urlbar.autocomplete.enabled", true);
pref("services.sync.prefs.sync.browser.urlbar.suggest.history.onlyTyped", true);
pref("browser.newtabpage.activity-stream.asrouter.providers.cfr", "{\"id\":\"cfr\",\"enabled\":true,\"type\":\"local\",\"localProvider\":\"CFRMessageProvider\",\"frequency\":{\"custom\":[{\"period\":\"daily\",\"cap\":1}]}}"); // prev: "{\"id\":\"cfr\",\"enabled\":false,\"type\":\"local\",\"localProvider\":\"CFRMessageProvider\",\"frequency\":{\"custom\":[{\"period\":\"daily\",\"cap\":1}]}}"
pref("browser.newtabpage.activity-stream.asrouter.providers.onboarding", "{\"id\":\"onboarding\",\"type\":\"local\",\"localProvider\":\"OnboardingMessageProvider\",\"enabled\":true,\"exclude\":[\"RETURN_TO_AMO_1\"]}"); // prev: "{\"id\":\"onboarding\",\"type\":\"local\",\"localProvider\":\"OnboardingMessageProvider\",\"enabled\":true}"
pref("browser.safebrowsing.provider.mozilla.lists", "base-track-digest256,mozstd-trackwhite-digest256,content-track-digest256,mozplugin-block-digest256,mozplugin2-block-digest256,block-flash-digest256,except-flash-digest256,allow-flashallow-digest256,except-flashallow-digest256,block-flashsubdoc-digest256,except-flashsubdoc-digest256,except-flashinfobar-digest256,ads-track-digest256,social-track-digest256,analytics-track-digest256"); // prev: "base-track-digest256,mozstd-trackwhite-digest256,content-track-digest256,mozplugin-block-digest256,mozplugin2-block-digest256,block-flash-digest256,except-flash-digest256,allow-flashallow-digest256,except-flashallow-digest256,block-flashsubdoc-digest256,except-flashsubdoc-digest256,except-flashinfobar-digest256,ads-track-digest256,social-track-digest256,analytics-track-digest256,fastblock1-track-digest256,fastblock1-trackwhite-digest256,fastblock2-track-digest256,fastblock2-trackwhite-digest256,fastblock3-track-digest256"
pref("devtools.flexboxinspector.enabled", true); // prev: false
pref("devtools.inspector.changes.enabled", true); // prev: false
pref("devtools.inspector.flexboxHighlighter.enabled", true); // prev: false
pref("devtools.netmonitor.visibleColumns", "[\"status\",\"method\",\"domain\",\"file\",\"cause\",\"type\",\"transferred\",\"contentSize\",\"waterfall\"]"); // prev: "[\"status\",\"method\",\"file\",\"domain\",\"cause\",\"type\",\"transferred\",\"contentSize\",\"waterfall\"]"
pref("devtools.webconsole.jsterm.reverse-search", true); // prev: false
pref("dom.keyboardevent.dispatch_during_composition", true); // prev: false
pref("dom.keyboardevent.keypress.dispatch_non_printable_keys_only_system_group_in_content", true); // prev: false
pref("dom.ua_widget.enabled", true); // prev: false
pref("font.name-list.sans-serif.zh-TW", "Arial, PMingLiU, MingLiU, MingLiU-ExtB, Microsoft JhengHei"); // prev: "Arial, Microsoft JhengHei, PMingLiU, MingLiU, MingLiU-ExtB"
pref("image.animated.generate-full-frames", true); // prev: false
pref("image.http.accept", "image/webp,*/*"); // prev: "*/*"
pref("intl.multilingual.enabled", true); // prev: false
pref("javascript.options.streams", true); // prev: false
pref("media.av1.enabled", true); // prev: false
pref("media.getusermedia.agc", 1); // prev: 3
pref("media.navigator.mediadatadecoder_h264_enabled", true); // prev: false
pref("network.http.accept.default", "text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8"); // prev: "text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8"
pref("network.http.send_window_size", 0); // prev: 1024
pref("privacy.trackingprotection.introURL", "https://www.mozilla.org/%LOCALE%/firefox/%VERSION%/content-blocking/start/"); // prev: "https://www.mozilla.org/%LOCALE%/firefox/%VERSION%/tracking-protection/start/"
pref("urlclassifier.disallow_completions", "test-malware-simple,test-harmful-simple,test-phish-simple,test-unwanted-simple,test-track-simple,test-trackwhite-simple,test-block-simple,goog-downloadwhite-digest256,base-track-digest256,mozstd-trackwhite-digest256,content-track-digest256,mozplugin-block-digest256,mozplugin2-block-digest256,block-flash-digest256,except-flash-digest256,allow-flashallow-digest256,except-flashallow-digest256,block-flashsubdoc-digest256,except-flashsubdoc-digest256,except-flashinfobar-digest256,goog-passwordwhite-proto,ads-track-digest256,social-track-digest256,analytics-track-digest256"); // prev: "test-malware-simple,test-harmful-simple,test-phish-simple,test-unwanted-simple,test-track-simple,test-trackwhite-simple,test-block-simple,goog-downloadwhite-digest256,base-track-digest256,mozstd-trackwhite-digest256,content-track-digest256,mozplugin-block-digest256,mozplugin2-block-digest256,block-flash-digest256,except-flash-digest256,allow-flashallow-digest256,except-flashallow-digest256,block-flashsubdoc-digest256,except-flashsubdoc-digest256,except-flashinfobar-digest256,goog-passwordwhite-proto,ads-track-digest256,social-track-digest256,analytics-track-digest256,fastblock1-track-digest256,fastblock1-trackwhite-digest256,fastblock2-track-digest256,fastblock2-trackwhite-digest256,fastblock3-track-digest256"
All 81 comments
apz.relative-update.enabled browser.contentblocking.control-center.ui.showAllowedLabels browser.contentblocking.control-center.ui.showBlockedLabels browser.contentblocking.cookies-site-data.ui.reject-trackers.enabled browser.contentblocking.cookies-site-data.ui.reject-trackers.recommended browser.contentblocking.enabled browser.contentblocking.fastblock.control-center.ui.enabled browser.contentblocking.fastblock.ui.enabled browser.contentblocking.global-toggle.enabled browser.contentblocking.rejecttrackers.ui.enabled browser.contentblocking.rejecttrackers.ui.recommended browser.contentblocking.trackingprotection.ui.enabled browser.contentblocking.ui.enabled browser.discovery.containers.enabled browser.discovery.enabled browser.discovery.sites browser.engagement.recent_visited_origins.expiry browser.fastblock.enabled browser.fastblock.limit browser.fastblock.timeout browser.fixup.hide_user_pass browser.safebrowsing.provider.mozilla.lists browser.schedulePressure.defaultCount browser.schedulePressure.enabled browser.schedulePressure.timeoutMs browser.security.newcerterrorpage.mitm.enabled browser.sessionstore.warnOnQuit browser.tabs.20FpsThrobber browser.tabs.30FpsThrobber browser.urlbar.autocomplete.enabled browser.urlbar.matchBehavior browser.urlbar.suggest.history.onlyTyped canvas.customfocusring.enabled canvas.imagebitmap_extensions.enabled devtools.aboutdebugging.network devtools.aboutdebugging.wifi devtools.console.stdout.chrome devtools.console.stdout.content devtools.flexboxinspector.enabled devtools.inspector.changes.enabled devtools.inspector.flexboxHighlighter.enabled devtools.inspector.fonteditor.enabled devtools.inspector.showUserAgentShadowRoots devtools.performance.profiler.sample-frequency-hz devtools.performance.profiler.sample-frequency-khz devtools.recordreplay.allowRepaintFailures devtools.recordreplay.includeSystemScripts devtools.recordreplay.timeline.enabled devtools.webconsole.jsterm.reverse-search dom.block_multiple_popups dom.browserElement.maxScreenshotDelayMS dom.compositionevent.text.dispatch_only_system_group_in_content dom.event.returnValue.enabled dom.ipc.tabs.createKillHardCrashReports dom.keyboardevent.dispatch_during_composition dom.keyboardevent.keypress.dispatch_non_printable_keys_only_system_group_in_content dom.keyboardevent.keypress.hack.dispatch_non_printable_keys dom.keyboardevent.keypress.hack.use_legacy_keycode_and_charcode dom.keyboardevent.keypress.set_keycode_and_charcode_to_same_value dom.payments.request.supportedRegions dom.performance.time_to_contentful_paint.enabled dom.reporting.cleanup.timeout dom.reporting.delivering.maxFailures dom.reporting.delivering.maxReports dom.reporting.delivering.timeout dom.reporting.enabled dom.reporting.featurePolicy.enabled dom.reporting.header.enabled dom.reporting.testing.enabled dom.security.featurePolicy.header.enabled dom.security.featurePolicy.webidl.enabled dom.sidebar.enabled dom.storage.next_gen dom.storage.shadow_writes dom.storage.snapshot_prefill dom.storage.snapshot_reusing dom.storage_access.auto_grants dom.storage_access.enabled dom.storage_access.max_concurrent_auto_grants dom.targetBlankNoOpener.enabled dom.ua_widget.enabled dom.webcomponents.customelements.enabled dom.webcomponents.shadowdom.enabled dom.window.event.enabled extensions.formautofill.reauth.enabled geo.provider.ms-windows-location gfx.omta.background-color gfx.webrender.dcomp-win-triple-buffering.enabled gfx.webrender.debug.slow-frame-indicator gfx.webrender.debug.texture-cache.clear-evicted gfx.webrender.picture-caching image.animated.decode-on-demand.recycle image.animated.generate-full-frames image.http.accept image.webp.enabled io.activity.intervalMilliseconds javascript.options.bigint javascript.options.streams layout.css.frames-timing.enabled layout.css.overflow-break.intrinsic-size layout.css.shape-outside.enabled layout.css.step-position-jump.enabled layout.css.text-align-unsafe-value.enabled media.av1.enabled media.av1.use-dav1d media.getusermedia.agc media.getusermedia.use_aec_mobile media.navigator.mediadatadecoder_enabled media.navigator.mediadatadecoder_h264_enabled media.navigator.mediadatadecoder_vpx_enabled media.rdd-process.enabled media.rdd-process.startup_timeout_ms media.test.video-suspend network.connectivity-service.DNSv4.domain network.connectivity-service.DNSv6.domain network.connectivity-service.enabled network.connectivity-service.IPv4.url network.connectivity-service.IPv6.url network.http.accept.default network.http.send_window_size network.http.spdy.enable-hpack-dump network.http.spdy.websockets network.IDN.blacklist_chars network.IDN.extra_allowed_chars network.IDN.extra_blocked_chars network.trr.custom_uri pdfium.enabled privacy.popups.maxReported privacy.restrict3rdpartystorage.partitionedHosts privacy.restrict3rdpartystorage.userInteractionRequiredForHosts privacy.trackingprotection.introCount security.strict_security_checks.enabled services.sync.prefs.sync.browser.contentblocking.enabled services.sync.prefs.sync.browser.urlbar.autocomplete.enabled services.sync.prefs.sync.browser.urlbar.suggest.history.onlyTyped services.sync.prefs.sync.privacy.fuzzyfox.clockgrainus services.sync.prefs.sync.privacy.fuzzyfox.enabled urlclassifier.disallow_completions urlclassifier.trackingAnnotationSkipURLssome bugzilla tickets
Bug 1453425 - Add relative scroll offset updates using nsGkAtoms::relative.
Bug 1511954 - Remove the "Allowed" label of content blocking categories and put it behind a pref.
Bug 1512166 - Show blocked labels by default, hide when there's an exception.
Bug 1511751 - Part 1 - Remove the "Blocked" labels of content blocking categories and put them behind a pref.
Bug 1502237 - Remove the pref for controlling whether the tracker cookie blocking setting would appear in the Cookies and Site Data drop-down
Bug 1487178 - Ensure that the Firefox configuration is up to date for the Content Blocking project;
Bug 1483378 - Part 5: Remove the old Cookies & Site Data UI;
Bug 1483378 - Part 4: Enable hiding the "reject trackers" menu item based on a preference;
Bug 1502221 - Remove the prefs for controlling whether a '(recommended)' suffix would be appended to tracker cookie blocking settings
Bug 1487178 - Ensure that the Firefox configuration is up to date for the Content Blocking project;
Bug 1483378 - Part 1: Update the Cookies and Site Data UI in the Preferences window;
Bug 1502757 - Stop syncing the browser.contentblocking.enabled pref
Bug 1486092 - Part 1: Move the browser.contentblocking.enabled pref to StaticPrefs;
Bug 1482281 - Sync contentblocking pref.
Bug 1476217 - Part 1 - Update Tracking Protection preferences for Content Blocking.
Bug 1501978 - Part 1: Stop honouring the browser.contentblocking.enabled pref in Gecko
Bug 1500208 - Disable FastBlock, hide FastBlock UI everywhere.
Bug 1502076 - Part 2: Remove the fastblock UI from the Control Centre
Bug 1496671 - Final pref changes for Content Blocking in Firefox 63.
Bug 1487178 - Ensure that the Firefox configuration is up to date for the Content Blocking project;
Bug 1485199 - Add prefs for hiding the other two categories in the Content Blocking section of the Control Centre;
Bug 1500208 - Disable FastBlock, hide FastBlock UI everywhere.
Bug 1502076 - Part 1: Remove the fastblock UI from Preferences
Bug 1496671 - Final pref changes for Content Blocking in Firefox 63.
Bug 1487178 - Ensure that the Firefox configuration is up to date for the Content Blocking project;
Bug 1486414 - Add prefs to hide the Trackers and FastBlock categories in the Content Blocking preferences;
Bug 1501977 - Remove global Content Blocking toggle in the main menu.
Bug 1496671 - Final pref changes for Content Blocking in Firefox 63.
Bug 1492175 - Add a pref for hiding the global content blocking toggle.
Bug 1509411 - Remove the browser.contentblocking.(trackingprotection|rejecttrackers).ui.enabled prefs
Bug 1493682 - Part 1: Introduce two new prefs for controlling whether the content blocking allow list would be honoured
Bug 1491061 - Part 4: Synchronize the default values of the essential prefs that content blocking depends on for all platforms;
Bug 1487178 - Ensure that the Firefox configuration is up to date for the Content Blocking project;
Bug 1484769 - Part 1: Update the Content Blocking section of the Preferences UI to add Third-Party Cookies options;
Bug 1502221 - Remove the prefs for controlling whether a '(recommended)' suffix would be appended to tracker cookie blocking settings
Bug 1487178 - Ensure that the Firefox configuration is up to date for the Content Blocking project;
Bug 1484769 - Part 1: Update the Content Blocking section of the Preferences UI to add Third-Party Cookies options;
Bug 1509411 - Remove the browser.contentblocking.(trackingprotection|rejecttrackers).ui.enabled prefs
Bug 1487178 - Ensure that the Firefox configuration is up to date for the Content Blocking project
Bug 1486414 - Add prefs to hide the Trackers and FastBlock categories in the Content Blocking preferences
Bug 1491061 - Part 1: Make Disable Protection honour both the Content Blocking UI pref and the pref controlling whether Third-Party Cookies section appears under Content Blocking UI;
Bug 1476217 - Part 1 - Update Tracking Protection preferences for Content Blocking.
Bug 1501286 - Part 5: Remove the browser.contentblocking.ui.enabled pref
Bug 1489531 Expose telemetry client_id hash to about:addons via cookie
Bug 1499470 - Provide option to opt-out of add-on recommendations
Bug 1489531 Expose telemetry client_id hash to about:addons via cookie
Bug 1489531 Expose telemetry client_id hash to about:addons via cookie
Bug 1509047 - Part 2: Add an API for measuring the number of unique origins visited in the past 24 hours
Bug 1500208 - Disable FastBlock, hide FastBlock UI everywhere
Bug 1489252 - Part 1: Move browser.fastblock.enabled to StaticPrefList.h
Bug 1502076 - Part 1: Remove the fastblock UI from Preferences
Bug 1480443 - Enable FastBlock by default on Nightly
Bug 1509555 - Part 2: Remove the core fastblock code
Bug 1500208 - Disable FastBlock, hide FastBlock UI everywhere
Bug 1509555 - Part 2: Remove the core fastblock code
Bug 1510580 - Remove browser.fixup.hide_user_pass pref
Bug 1509555 - Part 2: Remove the core fastblock code
Bug 1511095 - Remove SchedulePressure.jsm and the fallback loading throbber in the tabstrip.
Bug 1511095 - Remove SchedulePressure.jsm and the fallback loading throbber in the tabstrip.
Bug 1511095 - Remove SchedulePressure.jsm and the fallback loading throbber in the tabstrip.
Bug 1450784 - Add a new error page for MOZILLA_PKIX_ERROR_MITM_DETECTED.
Bug 1506173 - use separate pref for warning on quit with sessionstore enabled,
Bug 1511095 - Remove support for 20fps throbber.
Bug 1511095 - Remove support for the 30fps pref, and replace the loading.svg with the 30fps variant.
Bug 1502392 - Remove support for browser.urlbar.autocomplete.enabled.
Bug 1502728 - Actually remove matchBehavior from firefox.js.
Bug 1500108 - Remove the history.onlyTyped preference and behavior from the Address Bar.
Bug 1120371 - remove obsolete drawCustomFocusRing from Canvas2D. r=jrmuizel,
Bug 1500733 - Remove canvas.imagebitmap_extensions.enabled preference,
Bug 1489844 - Port DOMPrefs to StaticPrefs - part 1 - canvas_imagebitmap_extensions_enabled,
Bug 1507708 - Add default values for aboutdebugging wifi and network features;r=ladybenko
Bug 1482054 - Create module to manage network locations;r=daisuke
Bug 1507708 - Add default values for aboutdebugging wifi and network features;r=ladybenko
Bug 1480544 - Allow Console API to log messages on stdout,
Bug 1480544 - Allow Console API to log messages on stdout,
Bug 1509908 - Enabling the flexbox tools on all channels;
Bug 1492026 - Enable the flexbox panel in Nightly.
Bug 1470380 - Enable the first simple version of the flexbox highlighter (M0) in nightly only.
Bug 1491887 - Enable tracking CSS changes and the Changes panel for all release channels;
Bug 1508353 - [Track Changes] Enable track changes for nightly.
Bug 1478448 - (Part 1) Add pref for Track Changes feature.
Bug 1509908 - Enabling the flexbox tools on all channels;
Bug 1470380 - Enable the first simple version of the flexbox highlighter (M0) in nightly only.
Bug 1485324 - (Part 1) Remove pref for Font Editor and obsolete conditionals;
Bug 1485326 - Set the Font Editor pref to true for all channels.
Bug 1470375 - Set the font editor pref to true in Nightly builds.
Bug 1483660 - Hide UA Widget shadow root in inspector by default;r=ladybenko
Bug 1489745 - Convert the preference sample-frequency-khz to hz
Bug 1489745 - Convert the preference sample-frequency-khz to hz
Bug 1503750 - Add preference to allow crashing on repaint failures,
Bug 1505935 Part 3 - Add pref allowing system scripts to be exposed to the debugger,
Bug 1503703 - Style progress overlay.
Bug 1512257 - Enable reverse search on every channel;
Bug 1024913 - Add a preference to enable the reverse search UI;
Bug 675574 - Allow just 1 window.open() per event,
Bug 1503070 part 4. Remove getScreenshot() method from BrowserElement.
Bug 1288640 - Make TextComposition not dispatch eCompositionChange events (DOM "text" event) in the default group of web content
Bug 1510985 - Remove Event.returnValue temporarily in 64.
Bug 1499465 - Don't collect KillHard crashes on Beta or Release.
Bug 1496288 - part 2: Stop dispatching non-printable "keypress" events, set keyCode or charCode value to the other value when it's zero, start to dispatch "keydown" and "keyup" events during composition, and enable window.event by default
Bug 1496288 - part 2: Stop dispatching non-printable "keypress" events, set keyCode or charCode value to the other value when it's zero, start to dispatch "keydown" and "keyup" events during composition, and enable window.event by default
Bug 1496288 - part 1: Make blacklist prefs for keypress event behavior changes ride the train
Bug 1508503 - Remove medium.com from "dom.keyboardevent.keypress.hack.dispatch_non_printable_keys"
Bug 1510111 - Remove www.rememberthemilk.com from the blacklist of keyCode/charCode mirroring of keypress events
Bug 1502795 - Set keyCode or charCode of keypress event whose value is zero to the other's non-zero value by default again unless dispatched on known broken web apps
Bug 1479964 - Set KeyboardEvent.keyCode and KeyboardEvent.charCode to same value if the event is "keypress" event
Bug 1501102 - Move hard-coded 'supportedRegions' array to a pref to allow developers outside US/CA to test PaymentRequest.
Bug 1298381: Implement TimeToFirstContentfulPaint behind a pref
Bug 1508310 - Implement Report-to header support - part 12 - Cleanup out-of-date endpoints,
Bug 1508310 - Implement Report-to header support - part 5 - Report delivering,
Bug 1508310 - Implement Report-to header support - part 11 - Limit the number of reports,
Bug 1508310 - Implement Report-to header support - part 5 - Report delivering,
Bug 1492036 - Reporting API - part 1 - WebIDL,
Bug 1492036 - Reporting API - part 6 - FeaturePolicy,
Bug 1508310 - Implement Report-to header support - part 1 - Header parser,
Bug 1492036 - Reporting API - part 5 - tests,
Bug 1507230 - dom.security.featurePolicy.header.enabled pref controls the using of FeaturePolicy header,
Bug 1507230 - dom.security.featurePolicy.webidl.enabled pref controls the exposing of document.policy and HTMLIFrameElement.policy attributes,
Bug 1503551 - Make window.external.AddSearchProvider a dummy function,
Bug 1286798 - Part 54: Disable LSNG by default;
Bug 1286798 - Part 3: New basic (memory only) implementation of LocalStorage;
Bug 1286798 - Part 46: Add a pref for database shadowing;
Bug 1286798 - Part 40: Increase initial snapshot prefill to 16KB;
Bug 1286798 - Part 31: Support for lazy loading of items;
Bug 1286798 - Part 42: Implement snapshot reusing;
Bug 1509047 - Part 5: Add heuristics to the storage access API for automatically granting temporary session-scoped storage access without displaying a doorhanger prompt;
Bug 1498251 - Enable the Storage Access API in Nightly;
Bug 1515693 - Check allow-storage-access-by-user-activation sandbox flag only if StorageAccess API is enabled.
Bug 1509047 - Part 5: Add heuristics to the storage access API for automatically granting temporary session-scoped storage access without displaying a doorhanger prompt;
Bug 1503681 - rel=noopener implicit for target=_blank in anchor and area elements when no rel attribute is set,
Bug 1507894 - Enable UA Widget in beta/release
Bug 1484048 - Part V, Re-enable UA Widget on Desktop Nightly
Bug 1503019 - Part II, Remove dom.webcomponents.customelements.enabled pref
Bug 1503019 - Part I, Remove dom.webcomponents.shadowdom.enabled
Bug 1493869 - Put window.event behind a pref and disable it by default for release versions.
Bug 1471814 - Add a preference for {Document,Element}.getAnimations();
Bug 1496288 - part 2: Stop dispatching non-printable "keypress" events, set keyCode or charCode value to the other value when it's zero, start to dispatch "keydown" and "keyup" events during composition, and enable window.event by default
Bug 1503019 - Part I, Remove dom.webcomponents.shadowdom.enabled
Bug 1493869 - Put window.event behind a pref and disable it by default for release versions.
Bug 1510470 - Disable OS re-auth for credit cards by default.
Bug 1512161 - Use Windows & Mac system API for geolocation
Bug 1504065 - Run background-color animations on the compositor.
Bug 1500017 - Use triple buffer with DXGI_SWAP_EFFECT_FLIP_SEQUENTIAL SwapChain
Bug 1503730 - Add visual indicator for when WebRender frames record a CONTENT_FRAME_TIME of >200.
Bug 1507333 - Clear evicted cache entries when using the debug display.
Bug 1510725 - Add a pref to enable picture caching in WebRender.
Bug 1465619 - Part 11. Add support for recycling animated image frames.
Bug 1508393 - Enable animated images producing full frames by default.
Bug 1337111 - Part 5. Add pref to force decoding of full frames, disabled by default.
Bug 1503653 - Part 2. Enable WebP by default.
Bug 1294490 - Part 7. Enable WebP by default.
Bug 1503653 - Part 2. Enable WebP by default.
Bug 1294490 - Part 3. Implement WebP decoder.
Bug 1294490 - Part 7. Enable WebP by default.
Bug 1508257 - Remove io.activity.intervalMilliseconds -
Bug 1506542 - Add run-time flag to enable bigint support
Bug 1505122 - Enable ReadableStream for beta and release.
Bug 1389628 - Part 2: Enable Streams API by default.
Bug 1491939 - Part 4: Enable streams on a per-realm basis. Drop dom.streams.enabled and dom.workers.options.streams; use only javascript.options.streams.
Bug 1496619 - Part 1: Drop frames() timing function
Bug 1505786 - Implement overflow-wrap: anywhere.
Bug 1484587 - Put the behavior that overflow-wrap: break-word affecting intrinsic size behind a pref and disable it by default.
Bug 1504387 - Remove preference "layout.css.shape-outside.enabled".
Bug 1496619 - part 7: Implement steps(jump-*) functions
Bug 1500885 - Remove tests and other similar bits.
Bug 1452146 - flip av1 and rdd on for Win.
Bug 1452146 - flip av1 and rdd on for OSX and Win.
Bug 1493400 - Implement platform decoder for dav1d.
Bug 1509842 - Re-enable AGC by default.
Bug 1376873 - Updates to dom/media/, dom/media/systemservices and dom/media/webrtc;
Bug 1496714 - Enable AGC by default for getUserMedia.
Bug 1376873 - Updates to dom/media/, dom/media/systemservices and dom/media/webrtc;
Bug 1376873 - Updates to dom/media/, dom/media/systemservices and dom/media/webrtc;
Bug 1496529 - P8. Add media.navigator.mediadatadecoder_h264_enabled preference.
Bug 1505284 - P4. Split preferences to enable WebRTC with MediaDataDecoder.
Bug 1505284 - P2. Use system's h264 decoder for webrtc call.
Bug 1376873 - Updates to dom/media/, dom/media/systemservices and dom/media/webrtc;
Bug 1496529 - P8. Add media.navigator.mediadatadecoder_h264_enabled preference.
Bug 1508677 - Use playback's VP8/VP9 decoder for webrtc call on Nightly.
Bug 1505284 - P4. Split preferences to enable WebRTC with MediaDataDecoder.
Bug 1471535 - pt5 - Add prefs media.rdd-process.enabled and media.rdd-process.startup_timeout_ms.
Bug 1471535 - pt5 - Add prefs media.rdd-process.enabled and media.rdd-process.startup_timeout_ms.
Bug 1511235 - Part 3: Ensure video is visible before starting test.
Bug 1460537 - Connectivity Service - Add DNSv4 and DNSv6 checks
Bug 1460537 - Connectivity Service - Add DNSv4 and DNSv6 checks
Bug 1460537 - Connectivity Service - Add DNSv4 and DNSv6 checks
Bug 1502025 - Use captive portal endpoints for connectivity checks
Bug 1502025 - Use captive portal endpoints for connectivity checks
Bug 1507691 - Add image/webp to default HTTP Accept header.
Bug 1513135 - disable flow control of HTTP e10s back pressure
Bug 1505867 - Add pref for hpack table dumps.
Bug 1434137 - Implement websockets over http/2 - RFC 8441
Bug 1502097 - (Part 1) Move pref network.IDN.blacklist_chars to separate hardcoded file IDNCharacterBlocklist.inc
Bug 1502097 - (Part 1) Move pref network.IDN.blacklist_chars to separate hardcoded file IDNCharacterBlocklist.inc
Bug 1502097 - (Part 1) Move pref network.IDN.blacklist_chars to separate hardcoded file IDNCharacterBlocklist.inc
Bug 1495583 - Add a button to restore the default value for network.trr.uri preference.
Bug 1503537 - Get rid of the pdfium & mortar code
Bug 685828 - Limit displaying blocked popups in the front-end.
Bug 1505212 - Partitioned localStorage for 3rd party tracker pages, r=ehsan,
Bug 1507769 - User-interaction required before granting storage access for some 3rd party trackers,
Bug 1501286 - Part 2: Remove support for tracking protection UI from Control Centre
Bug 1498526 - add in user pref to prevent loading implied triggeringPrincipal loads for dev and nightly builds.
Bug 1502757 - Stop syncing the browser.contentblocking.enabled pref
Bug 1482281 - Sync contentblocking pref.
Bug 1502392 - Remove support for browser.urlbar.autocomplete.enabled.
Bug 1500108 - Remove the history.onlyTyped preference and behavior from the Address Bar.
Bug 1505109 - Disable fuzzyfox pref syncing by default
Bug 1432429 - Add FuzzyFox class and prefs.
Bug 1505109 - Disable fuzzyfox pref syncing by default
Bug 1432429 - Add FuzzyFox class and prefs.
Bug 1509555 - Part 2: Remove the core fastblock code
Bug 1507013 - Add a site-specific workaround for Google Recaptcha to improve the user experience of using it with the new cookie policy;
network.connectivity-service.* is really a bloated feature. All those checks should be done outside of a browser.
dom.payments.request.supportedRegions Web Payments:
https://firefox-source-docs.mozilla.org/browser/components/payments/docs/index.html
https://wiki.mozilla.org/Firefox/Features/Web_Payments
dom.reporting.*
The Reporting API defines a new HTTP header Report-To that gives web developers a way to specify server endpoints for the browser to send warnings and errors to.
See: https://developers.google.com/web/updates/2018/09/reportingapi
am on 65b12 .. was waiting for a newer update before I move shit round in OP. Should I just start anyway? @earthlng
65.0b12 changes since 65.0b8
new
pref("toolkit.tabbox.switchByScrolling", false);
removed, renamed or hidden
pref("dom.event.returnValue.enabled", false);
changed
pref("browser.newtabpage.activity-stream.asrouter.providers.cfr", "{\"id\":\"cfr\",\"enabled\":true,\"type\":\"local\",\"localProvider\":\"CFRMessageProvider\",\"frequency\":{\"custom\":[{\"period\":\"daily\",\"cap\":1}]}}"); // prev: "{\"id\":\"cfr\",\"enabled\":false,\"type\":\"local\",\"localProvider\":\"CFRMessageProvider\",\"frequency\":{\"custom\":[{\"period\":\"daily\",\"cap\":1}]}}"
pref("browser.newtabpage.activity-stream.asrouter.providers.onboarding", "{\"id\":\"onboarding\",\"type\":\"local\",\"localProvider\":\"OnboardingMessageProvider\",\"enabled\":true,\"exclude\":[\"RETURN_TO_AMO_1\"]}"); // prev: "{\"id\":\"onboarding\",\"type\":\"local\",\"localProvider\":\"OnboardingMessageProvider\",\"enabled\":true}"
pref("browser.newtabpage.activity-stream.asrouter.providers.snippets", "{\"id\":\"snippets\",\"enabled\":true,\"type\":\"remote\",\"url\":\"https://snippets.cdn.mozilla.net/%STARTPAGE_VERSION%/%NAME%/%VERSION%/%APPBUILDID%/%BUILD_TARGET%/%LOCALE%/%CHANNEL%/%OS_VERSION%/%DISTRIBUTION%/%DISTRIBUTION_VERSION%/\",\"updateCycleInMs\":14400000}"); // prev: "{\"id\":\"snippets\",\"enabled\":false,\"type\":\"remote\",\"url\":\"https://snippets.cdn.mozilla.net/%STARTPAGE_VERSION%/%NAME%/%VERSION%/%APPBUILDID%/%BUILD_TARGET%/%LOCALE%/%CHANNEL%/%OS_VERSION%/%DISTRIBUTION%/%DISTRIBUTION_VERSION%/\",\"updateCycleInMs\":14400000}"
pref("dom.keyboardevent.keypress.set_keycode_and_charcode_to_same_value", true); // prev: false
pref("dom.window.event.enabled", true); // prev: false
pref("intl.multilingual.enabled", true); // prev: false
pref("privacy.trackingprotection.introURL", "https://www.mozilla.org/%LOCALE%/firefox/%VERSION%/content-blocking/start/"); // prev: "https://www.mozilla.org/%LOCALE%/firefox/%VERSION%/tracking-protection/start/"
EDIT: updated 1st post
moved a heap of items from new to ignore: if anything in ignore looks like it should be revisited, sing out
OT: interesting way to hide a malicious URL so it's not exposed / detected until both the js is run and the image is present - https://arstechnica.com/information-technology/2019/01/malvertisers-target-mac-uses-with-stenographic-code-stashed-in-images/
pref("dom.payments.request.supportedRegions", "US,CA");
Users have to add country codes to make it eventually work (geo info given):https://github.com/mdn/browser-compat-data/issues/3164
oooh .. it's almost here .. is anyone in a hurry? Or can I leave this for a few days
@Thorin-Oakenpants It seems someone is lazy? 😯
I have shit to do .. like drink beer .. and as usual .. it's always me and earthlng ... or nothing happens
@Thorin-Oakenpants
I have shit to do .. like drink beer
okay 🙂
in fact, there is not much to add. 1-2 hours of work.
but I not insist
65.0 changes since 65.0b12
changed
pref("app.update.channel", "beta"); // prev: "release"
pref("app.update.url.details", "https://www.mozilla.org/%LOCALE%/firefox/beta/notes"); // prev: "https://www.mozilla.org/%LOCALE%/firefox/notes"
pref("app.update.url.manual", "https://www.mozilla.org/firefox/beta"); // prev: "https://www.mozilla.org/firefox/"
pref("extensions.webcompat-reporter.enabled", true); // prev: false
pref("font.name-list.sans-serif.zh-TW", "Arial, PMingLiU, MingLiU, MingLiU-ExtB, Microsoft JhengHei"); // prev: "Arial, Microsoft JhengHei, PMingLiU, MingLiU, MingLiU-ExtB"
pref("toolkit.telemetry.enabled", true); // prev: false
EDIT: updated 1st post
@earthlng
pref("dom.push.alwaysConnect", true); // prev: false
changed?
I have so and remained "false." firefox 65

Oops, you're right. I forgot to block its internet access and it must have installed some shield studies or whatnot which affected the pref defaults. I did the diff kind of in the background while doing something else - my bad, sorry.
browser.newtabpage.activity-stream.improvesearch.topSiteSearchShortcuts.searchEngines was also changed by something like that and the default (with internet access blocked) is still empty string.
I'll update the list. Thanks @bogachenko
@overdodactyl and others, see bug https://bugzilla.mozilla.org/show_bug.cgi?id=1504766 - basically in windows 10 the OS takes over title bar colors (so everything on the top except the current tab ends up with your windows theme)
The solution was to go to Windows settings > personalization > colors. and then in “show accent color on the following surfaces” untick the option “title bars”. But of course that's not a proper solution - maybe you want that *except for firefox.
Anyway: here is the answer: from comment 24 on the linked bugzilla
stick in 5000 under appearance?
// user_pref("ui.-moz-win-accentcolor", "#202340"); // [FF65+] [HIDDEN PREF]
// user_pref("ui.-moz-win-accentcolortext, "#f9f9fa"); // [FF65+] [HIDDEN PREF]
// ^ override Windows 10 accent color on Firefox's title bar
// ^ default: #202340, #f9f9fa | light: #e3e4e6, #18191a | dark: #0c0c0d, #f9f9fa
@Thorin-Oakenpants So what about the update userjs? Tomorrow already has come.
~I've had a night. Crappy time zone. uh~
network.connectivity-service.enabled- disable under Quiet Fox? just the master switch should be enoughnetwork.http.spdy.websockets- maybe disable this together with the other spdy stuff, just in casesecurity.strict_security_checks.enabled- currently being tested in Nightly "for one cycle" (until they land it in Release?). Something to do with triggering principals. I think we can just wait until it lands in Release. Shouldn't be much of a risk in enabling it already either though but IDK how much potential breakage it could cause. I'll enable it in my main FF and see how it goes
I think we could also force-disable all the Reporting API shit even though it's still default false in Release atm
For the time being I've set,
// Network Connectivity Services -- unneeded entries unless you use Sync account and maybe Push notifcations
// These FF 65 entries go against the security principle of a reduced attack surface, as there's a DNS Hijack opportunity.
pref("network.connectivity-service.enabled", false);
pref("network.connectivity-service.DNSv4.domain", "");
pref("network.connectivity-service.DNSv6.domain", "");
pref("network.connectivity-service.IPv4.url", "http://0.0.0.0");
pref("network.connectivity-service.IPv6.url", "http://0.0.0.0");
// Add-on recommendations
pref("browser.discovery.enabled", false);
pref("browser.discovery.containers.enabled", false);
pref("browser.discovery.sites", "");
// Storage Access API
pref("dom.storage_access.enabled", false);
// More
pref("network.http.spdy.websockets", false);
// Unknown
// pref("privacy.restrict3rdpartystorage.partitionedHosts", "accounts.google.com/o/oauth2/");
// pref("privacy.restrict3rdpartystorage.userInteractionRequiredForHosts", "");
The Srorage Access API in particular disturbs me, I can't understand its pertinence.
Network Connectivity Services -- unneeded entries unless you use Sync account and maybe Push notifcations
Sorry, I haven't even had time to look up what this is. Are you saying it's only if you use Sync (and maybe push notification FROM sync). If that's the case then we don't need to add them at all, because sync is an end user choice to set up an account etc, and we already don't mess with sync
I confess having borrowed the comments related to Network Connectivity Services at https://github.com/intika/Librefox/issues/102, I only chose the values accordingly.
All this is temporary, just trying to advance, need experts' views.
Dom Reporting API : quoting @Atavic
dom.reporting.*
The Reporting API defines a new HTTP header Report-To that gives web developers a way to specify server endpoints for the browser to send warnings and errors to.
See: https://developers.google.com/web/updates/2018/09/reportingapi
No idea about this one, new kid in town?
^^ no worries. We'll scope it out. I always check the source rather than rely on 3rd parties (unless they have a proven record like gorhill, earthlng
edit: yeah, OK .. that librefox issue simply points to two more librefox issues and none of them address the new prefs
I always check the source rather than rely on 3rd parties (unless they have a proven record like gorhill, earthlng
That's also what's most appreciated here. You guys wouldn't be here, referring to roots rather than to leaves, I'd (we'd) have to compare many settings with often different values/advice and most often no explanations. Objectivity is the word, here. Great work, I'd like to be able to bring more substantial comments.
Network Connectivity Services start a DNS query and an HTTP query to check if browser is online. Who's in need to such checks? The user or mozilla? I'll skip this 100%
HTTP query is not secured.
network.connectivity-service.enabled - I've checked the source code and with this set to false, the other 4 prefs are never used. I'll move this one to the todo list and the other 4 to "ignore".
browser.discovery.enabled is tied to datareporting.healthreport.uploadEnabled and both need to be enabled for Discovery to work.
There's also a new UI setting for this under about:preferences#privacy "Firefox Data Collection and Use" titled "Allow Firefox to make personalized extension recommendations" but IDK if that setting already exists in FF65 (I'm on 66 dev edition). Can somebody on FF65 confirm please?
The "container" pref (browser.discovery.containers.enabled) just makes sure that the cookie is set in the correct container if you visit AMO in a container tab so I'd say we can safely ignore that pref.
network.connectivity-service.enabled - I've checked the source code and with this set to false, the other 4 prefs are never used. I'll move this one to the todo list and the other 4 to "ignore".
OK.
browser.discovery.enabled is tied to datareporting.healthreport.uploadEnabled and both need to be enabled for Discovery to work.
OK
"Firefox Data Collection and Use" : available here on FF65
Extension Recommendations, “(Contextual Feature Recommendation) CFR is a system that proactively delivers personalized Firefox feature and extension recommendations to users based on their behavior.”
Preference value : browser.newtabpage.activity-stream.asrouterExperimentEnabled
I had it already set to false (as a lockPref) so it's grayed out here.
That's not the same. One is CFR and the other one is called Discovery.
Do you have "Allow Firefox to make personalized extension recommendations" under "Firefox Data Collection and Use" in FF65?
FYI: the CFR UI setting is "Recommend extensions as you browse" under about:preferences#general
FYI number2: browser.newtabpage.activity-stream.asrouterExperimentEnabled is long gone :)
Do you have "Allow Firefox to make personalized extension recommendations" under "Firefox Data Collection and Use" in FF65?
Yes and none is ticked. I will check again about ticks on a vanilla, later today... and report back.
Do you have "Allow Firefox to make personalized extension recommendations" under "Firefox Data Collection and Use" in FF65?
Yes, "Allow Firefox to make personalized extension recommendations" but under about:preferences#Privacy & Security and it's grayed out here.
FYI number2: browser.newtabpage.activity-stream.asrouterExperimentEnabled is long gone :)
I've just commented it and above remained grayed out, so I just don't know which of my settings disables it :=)
i'm learning the hard way... there are indeed two Firefox 65 different options when I was aware only of the second:
about:preferences / General / Browsing
Recommend extensions as you browse
about:preferences / Privacy & security / Firefox Data Collection and Use
Allow Firefox to make personalized extension recommendations
Both here are grayed out and blocked (I use config.js with lockPrefs) and I cannot manage to find out which setting blocks them...
Good Heavens, this is confusing.
I just don't know which of my settings disables it
you can search https://raw.githubusercontent.com/ghacksuserjs/ghacks-user.js/master/user.js for "Recommend extensions as you browse" ;)
@crssi
Yes and none is ticked
did you already disable the new discovery pref maybe? Or did it change to false automatically because the telemetry pref is disabled?
you can search https://raw.githubusercontent.com/ghacksuserjs/ghacks-user.js/master/user.js for "Recommend extensions as you browse" ;)
OK, that's pref("browser.newtabpage.activity-stream.asrouter.userprefs.cfr", false);
Remains the latter, confusing, grayed/blocked here for a setting I ignore. I know it's disabled by default but here it's disbled and grayed out which means I have a lockpref enforcing it to off:
about:preferences / Privacy & security / Firefox Data Collection and Use
Allow Firefox to make personalized extension recommendations
Thanks for the smiles, I'm walking on myself as we say in French.
There's a bit of UI "trickery" going on here similar to the solution in https://bugzilla.mozilla.org/show_bug.cgi?id=1447226

That new UI option is controlled by browser.discovery.enabled. Go ahead and reset it to true in about:config, reload about:preferences#privacy and it will make no difference .. if the top checkbox is not ticked, the two sub checkboxes will also be not ticked, regardless of what the pref says
As earthlng points out, that parent option is datareporting.healthreport.uploadEnabled. I don't know if it was always the case, but shield studies are now a sub-option. So too is this new one. The UI is one thing, the code is another. They're getting better at this, trust me. Earthlng just checked the new option code and confirmed nothing happens unless healhreport is renabled
If you use the UI to check healthreport, it auto checks the personalized extensions. If you set healthreport via about:config (or user.js), then it doesn't auto check change the personalized extensions (you have to close and reopen the options page for the changes to show)
Anyway, it is entirely possible to get a confusing state of values.
I still think we should include this and clean up shield studies info, that both have no effect of healthreport is disabled
Edit: this is the LearnMore link: https://support.mozilla.org/kb/personalized-extension-recommendations
A real bag of bones.
nothing happens unless healhreport
[datareporting.healthreport.uploadEnabled] is renabled
Good, we certainly won't re-enable it
The UI is one thing, the code is another.
Bag of bones.
Which means, if I understand correctly, that to be able to choose the value of
about:preferences / Privacy & security / Firefox Data Collection and Use /
_Allow Firefox to make personalized extension recommendations_
we need to have
datareporting.healthreport.uploadEnabled = true AND browser.discovery.enabled = true
Well, things are getting clearer. Light amid the darkness.
See: https://old.reddit.com/r/firefox/comments/alnn3f/storageaccessapi_permissions/effg5tp/ and the subsequent original thread
So storage access api is (for now) going to fill up and keep filling up with every site you visit
I actually closed Firefox, deleted my permissions.sqlite, restarted Firefox, and added back in 12 cookie permissions .. e.g I would just visit github, change the setting via the icon panel doropdown, reload the page and I was logged back in. I don't think I had any other permission exceptions TBH other than cookie ones.
My permissions.sqlite was 4.5mb (had a shitload of sites listed to block popup, image, install etc? NFI where they came from - maybe spybot search and destroy) .. now it's a super speedy 96kb
I've disabled this Storage Access API: pref("dom.storage_access.enabled", false);
My permissions.sqlite is now 160KB, I use SpywareBlaster but not its Mozilla Firefox protection which basically adds sites to have their cookies blocked, many sites which make finding my exceptions a hard work (another thing Mozilla could do is adding a search in the exceptions list...). Many exceptions here because I block cookies by default and add session only cookie permissions when site won't load without, and cookies allowed for three sites only. I read the #622 post on the power of cookie permissions, stunning.
Internet is nice but it certainly isn't as calm and relaxing as a Sunday in the countryside. Infernal machine it is.
All my software is portable (including SpywareBlaster : it's not hard to make it portable), and I do use it on client machines when applicable - e.g have to fix issues due to malware. I updated Spybot a couple of months ago, and did a one off yearly immunization with it on my own machine. I guess I was busy/tired and didn't register that FF would get bloated.
@earthlng
Allow Firefox to send technical and interaction data to Mozilla
datareporting.healthreport.uploadEnabled
Allow Firefox to install and run studies
app.shield.optoutstudies.enabled
Allow Firefox to install and run studies
browser.discovery.enabled
Allow Firefox to send backlogged crash reports on your behalf
browser.crashReports.unsubmittedCheck.autoSubmit2
True= ticked
On Nilla first 3 are True= ticked and the last is False= unticked
If the first is False= unticked then the next two are also unticked
Cheers
I've used Spybot S&D for years but abandoned it when it seemed to me it was getting bloated. I think its free edition is now rather limited compared to paid plans. Too heavy for me, even the free version. Moreover I recall its hosts entries problematic to deal with when one's hosts are managed by an integration tool such as Hostsman.
I read the #622 post on the power of cookie permissions, stunning.
I don't think it was always the case. The thing is they want everything to go thru an urlClassifier (or something) and thru content blocking first, and this then controls all persistent tracking data - so basically it's now all in place, that a cookie permission controls all data. And the next step is turning on NGLS (next gen local storage) and better quota management.
This is why you're seeing what cookies to accept are now under "Content Blocking" followed by a "Cookies & Site Data" section. All the cookie stuff used to be under "History".
As far as i'm concerned my cookie policy became radical (blocked by default) when cookies actually became the passport so to say of content blocking as mentioned above by you. The number of sites which take advantage of cookie permission to lay data in the user's localStorage and/or in his IndexedDB is relevant of the power given to websites, intentionally or not. In the older days I wouldn't even have imagined blocking cookies systematically.
My opinion is that laying data on a user's disk has always been an aim. Officially to make things quicker (quicker, when broadband is rising everywhere?) but in reality aimed at tracking. I'm a Firefox user and defender so to say but I really believe integrating cookies permissions in a global Content Blocking scheme was and remains more than a mistake: a fault.
Fortunately Firefox (still) includes the means to react, even if it's getting more and more complex if not complicated, not to mention technically unskilled Firefox users (is it legitimate to use a browser which is out of the box optimized for privacy without having to enter an Operations Center such as here in order to surf quietly?).
Anyway, for those of us, even partially (un) qualified as myself and others of course, given we have the time (I do, not everyone does), determination and the acceptation of a minimum of effort, we manage, thanks to places and people as here, to keep the best, improve the improvable and shut the worst of a browser's features.
I've been default deny cookies for probably at least 5 years. Excluding sites I need to log into (e.g bank, here) .. I've only ever come across a handful that actually really needed cookie permissions to work.
The problem is IDB (which is also used by service workers) cannot be cleared by host or time range (except time range: all). So it really comes down to clearing that on close, and realizing that you can have a session persistent storage in those areas. This is why I think cookie extensions are useless - what's the point in allowing all cookies all the time and cleaning up all the time, and leaving orphaned data ... sheeshus .. just think of the hundreds on thousands .. or rather millions . of cookie related shit I never had to deal with - read, writes, and OMG the tracking
Here's my decentraleyes for comparison: 300k of a small set of cdn files - that's over 4 to 5 years I guess since I installed it

Here's uBO : 2.2million requests- thats' since around FF54/55 (I started a clean counter etc when I set it up, on the way to moving from legacy extensions to web extensions)

So imagine what I saved in the last 4 or 5 years by denying cookies by default.
I actually like the approach of going thru cookies (all they did was extend it to also control some workers - i.e cookies have always AFAIK controlled local storage and IDB). The problem here is that you can't allow cookies but selectively deny IDB - in PB Mode it's auto denied. But the others are all fine. You can block service workers (e.g pref or in uMatrix), and you can clear local Storage by host.
Mozilla are close. We'll see how NGLS goes
network.connectivity-service.enabled- disable under Quiet Fox? just the master switch should be enough
I searched and searched, checked out DXR, scoped out mercurial, used my google-fu ,, and I cannot find the ticket this was introduced. Did special Core>Networking searches on bugzilla, and MOAR. The best I can come up with is this
https://bugzilla.mozilla.org/show_bug.cgi?id=1460537
- > We want a service similar to the captive portal check that will provide information about the network path to a fixed endpoint.
>
> This will let us know if we can use features such as TLS 1.3, IPv6, etc - that might not be supported by the network or they might be blocked by middleboxes.
- > We want a service similar to the captive portal check that will provide information about the network path to a fixed endpoint.
https://bugzilla.mozilla.org/show_bug.cgi?id=1502025
- use captive portal service to perform connectivity
I'm still not sure exactly what this is trying to do. Not the IPv6/IPv6 bits, but the actual Connectivity Service.
geo.provider.ms-windows-location was added in FF38 - https://bugzilla.mozilla.org/show_bug.cgi?id=512407
This is the bugzilla linked to (2nd post): https://bugzilla.mozilla.org/show_bug.cgi?id=1512161 but I don't see this pref getting flipped in there. In https://bugzilla.mozilla.org/show_bug.cgi?id=1513186 - they refer to it as MLS. I'm guessing that means Mozilla Location Service. But all those zillas are not about this pref, right?
What am I missing here? The pref is "ms-windows"
Edit: just to add some info: https://bugzilla.mozilla.org/show_bug.cgi?id=1322477#c5
The
geolocation providercan be Google, Apple, Windows, or Mozilla; it is the service we query for location. It is different depending on the OS. It looks like on windows we are using Mozilla Location Service (since if ms-windows-location is false, we use Mozilla's):
also note in the same comment
Can you try set about:config
geo.provider.ms-windows-location=trueand report if that fixed the problem? (btw, on windows older than 8 this setting is ignored).
^^ https://bugzilla.mozilla.org/show_bug.cgi?id=1512161 is definitely the one.
It got changed/activated by them removing and changing the if blocks around these prefs (and the prefs within): https://hg.mozilla.org/mozilla-central/rev/6de1ea2f0c0f#l1.16
ifndef EARLY_BETA_OR_EARLIER means if **not** early beta or earlier ie nightly which effectively made that block apply to Release+later betas. Now they removed that and also changed #if defined(XP_WIN) && defined(NIGHTLY_BUILD) to #ifdef XP_WIN ie it's no longer just active in Nightly on Windows.
geo.provider.use_gpsd seems to be equivalent to ms-location but on GTK systems (linux?) and geo.provider.use_corelocation is for Macs
on windows older than 8 this setting is ignored
good to know, thanks! :+1:
on windows older than 8 this setting is ignored
That is from a 2 yr old comment, so I'm not 100% sure if that is still the case
Well fuck .. dom.storage_access.enabled = false does nothing to stop permissions.sqlite filling up
LOL, at least we can remove it again then, right? I use 1006 so this probably doesn't affect me :) (I'll have to check...)
rub it in ... I might clean mine out again and keep a copy for periodic replacement. I don't think my cookies list has changed for years
Edit: already updated the user.js .. NFI why you don't get notifications
where do you want dom.reporting?
it's similar to 2681 (now under 9999) but reporting is not really of any security benefit to users, so I'd say still under MISC but maybe 2621 or so? waddaya think?
/* 2621: disable Reporting API [FF65+]
* Stores reports and endpoints in a reporting cache, which are then queued and sent via
* the HTTP header "Report-To" to endpoints. A report is a collection of **arbitrary** data.
* [1] https://w3c.github.io/reporting/ ***/
user_pref("dom.reporting.enabled", false); // [DEFAULT: false]
I don't quite like it, it needs MOAR cowbell, better info and to sound scarier
- Endpoint(s): So I am to understand that a 1stparty.com can send a report(s) to multiple endpoints including 3rd party?
- Reporting Cache: is this a global cache? Where is this cache? Also, I wonder if they applied origin attributes.
- Reporting Observer .. yay, more observers: the Inner Party would be proud
Also the link could be https://w3c.github.io/reporting/#security or https://w3c.github.io/reporting/#privacy. The #security one seems better because its super short and you can instantly see the privacy section, and if we get our little description great again, then this would be better than linking to the top of the doc
Let's just ignore the reporting api for now. When they enable it and have an MDN page ready, we can do some testing and see if it's worse than what JS can do already anyway. ie sending arbitrary data
earthlng, 3 days ago
I think we could also force-disable all the Reporting API shit even though it's still default false in Release atm
earthling, 2 hrs ago after I read about it and wrote a shitty draft
Let's just ignore the reporting api for now
OK, done. Left it in OP under FYI with the w3c link
Endpoints follow Network Error Logging policies: they also list the IP address of the server visited by the user agent.
Also see: What goes in a HPKP violation report? ...scroll down near the bottom.
Inner Party is mainly Google, see editors and chromestatus.
1495583 There is no need to add network.trr.custom_uri to the user.js. Here's how it works
DoH is controlled by network.trr.mode - i.e you check the option to used DNS over HTTP.
If you wish to use a custom URI then you need to check the radio option "custom" and stick in a value (note: you need to OK out of the connections settings panel for changes to take place and prefs to change)
What happens is both network.trr.custom_uri and network.trr.uri get set to the same value. Here's a pic for those who can't read
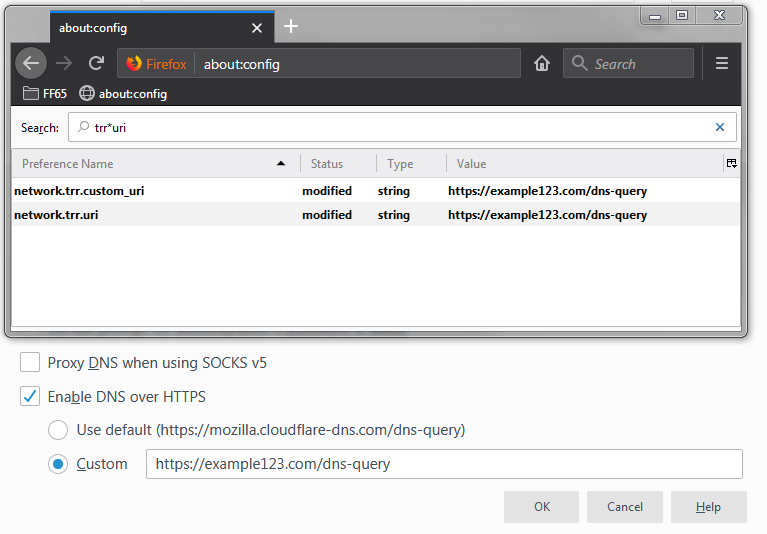
If you change your option to use the default, then network.trr.uri is reset, but network.trr.custom_uri is retained so it's there if you need it again. There is no pref to "use custom", it's just a field to hold the URI. The actual URI used is always network.trr.uri (AFAIK)
Update:
I just want to check something: if the UI text changes: use default (this bit listing the uri) - No, it doesn't. Edit network.trr.uri to whatever you like, e.g https://456.example.com/dns-query, and then bring up the connection settings panel, and it will still show the mozilla cloudflare one.
@earthlng : I think we should remove these from 0707:
// user_pref("network.trr.bootstrapAddress", "");
// user_pref("network.trr.uri", "");
The first is default blank, the second is potentially misleading e.g if someone uses it to set a custom uri. Misleading at least in the UI since the cloiudflare uri is hardcoded text. Possible misleading in that the new pref being something different might even break something - not worth even checking (but my gut instinct is that it wouldn't)
We can add a [SETTING] tag for DoH, and/or a warning tag that you should set your custom URI from the settings as it makes changes to multiple prefs
/* 0707: disable (or setup) DNS-over-HTTPS (DoH) [FF60+]
* TRR = Trusted Recursive Resolver
* .mode: 0=off, 1=race, 2=TRR first, 3=TRR only, 4=race for stats but always use native result
* To use a custom URI, use the Connection Settings panel, as it involves multiple prefs
* [WARNING] DoH bypasses hosts and gives info to yet another party (e.g. Cloudflare)
* [SETTING] General>Network Settings>Settings>Enable DNS over HTTPS
* [1] https://www.ghacks.net/2018/04/02/configure-dns-over-https-in-firefox/
* [2] https://hacks.mozilla.org/2018/05/a-cartoon-intro-to-dns-over-https/ ***/
// user_pref("network.trr.mode", 0);
nits? - edit: see PR #631
PS: moving the new pref to ignore
re: DoH, IMO we should just add the new pref and keep all the old ones as well. The new custom one is mostly used for display purposes in the UI but if you have setup the 3 "old" ones and not set the new 1 and then go into the UI and end up clicking OK while "custom" is selected, it will update .trr.uri with the empty string from custom_uri and break your DoH config.
end up clicking OK while "custom" is select ... break your DoH config
which is exactly why just adding the new pref is not good enough - you need to explain that you need to set both the same
Here's what I have left: basically 5 items (restrict3rdparty as one item)
new
- pref("network.connectivity-service.enabled", true);
- still NFI what this does exactly or where to put it or if it's even an issue
- pref("dom.targetBlankNoOpener.enabled", false); - 1503681
- you guys want to add it. I'd rather drop it and it becomes default in 67 and we don't even need to add it. If we add it then it needs to be qualified as not being comprehensive (and I don't know how to word that) and we should point out
window.opener be gone
- you guys want to add it. I'd rather drop it and it becomes default in 67 and we don't even need to add it. If we add it then it needs to be qualified as not being comprehensive (and I don't know how to word that) and we should point out
- pref("security.strict_security_checks.enabled", false);
- NFI, big E said he would test it for a while.
- pref("privacy.restrict3rdpartystorage.partitionedHosts", "accounts.google.com/o/oauth2/");
- pref("privacy.restrict3rdpartystorage.userInteractionRequiredForHosts", "");
- NFI: I have yet to even look them up
changed
- pref("geo.provider.ms-windows-location", true); // prev: false - 1495583
- still NFI what we should do with this
Edit: I'm seeing a pattern of NFI emerging
pref("privacy.restrict3rdpartystorage.partitionedHosts", "accounts.google.com/o/oauth2/");
https://bugzilla.mozilla.org/show_bug.cgi?id=1505212
Partitioned localStorage for 3rd party tracker pages
pref("privacy.restrict3rdpartystorage.userInteractionRequiredForHosts", "");
https://bugzilla.mozilla.org/show_bug.cgi?id=1507769
User-interaction required before granting storage access for some 3rd party trackers
are both to do with TP - moving to ignore
pref("security.strict_security_checks.enabled", false);
https://bugzilla.mozilla.org/show_bug.cgi?id=1498526
add in user pref to prevent loading implied triggeringPrincipal loads for dev and nightly builds
they're still testing it in dev and nightly (as E pointed out), so this is going to ignore be moved into the FYI section for visibility but we'll do nothing with it for now
network.connectivity-service.enabledis just making (mostly) unnecessary and unasked-for requests.
It fits best under Quiet Fox but it's also very similar to captive-portal checks and I just saw that we have that one under 0600. 0300 is already pretty long and 0604 is free and right after captive-portal so we could use that or maybe move both to 03xx somewhere.dom.targetBlankNoOpener.enabled- we can add it without much or any explanation IMO.
In the other issue a user suggested the titleAdd rel="noopener" automatically to links that use target="_blank". Mozilla titled their commitsrel=noopener implicit for target=_blank in anchor and area elements when no rel attribute is set. I like the one the devs used but maybe you can come up with a mix of both or something.geo.provider.ms-windows-location- there are 3 prefs for this, one for each OS. The diff only lists the 1 for Windows because that's what the diffs are based on. IDK what to do with it either. Might be best to disable all of them in the Geo section because while you might not mind letting your OS know your geo location, sharing it with the browser is maybe not always desirable.
maybe the title could just be "enable window.opener protection" (or "enable builtin (limited) window.opener protection") to keep it simple and then followed by a 1st line "Makes rel=noopener implicit for target=_blank in anchor and area elements when no rel attribute is set".
IDK if we need to mention anything else, it probably just makes it too confusing (fe. some examples would be that webadmins can still use rel="opener" to enable openers for certain links, some elements like <form> and <base> are not protected, window.open() is not "protected", (etc?))
oh, and I moved pref("network.trr.custom_uri", ""); back from ignore - see ya tomorrah .. won;t be finishing this today that's for sure
@earthlng we should finish this, but I don't know what to do I know what to do
dom.targetBlankNoOpener.enabled
- The only reason I would include it, is to point out that it's not a cure-all and to also point to the superior solution of your extension. If I can't do both of those, then fuck it, I would prefer ignoring this and just let Firefox flip it in 67
- waiting on you to OK having your extension linked to
- if we add it, then need you to word that's it not a cure-all (I'm not technical enough)
- so this is all yours right now :trollface:
network.connectivity-service.enabled
- this should be easy, Just shove it under quiet fox as
0609. The captive portal thing was only in a test, I think. I don't quite understand it all. Anyway, this is good enough for me. - :heavy_check_mark: DONE
/* 0609: disable Network Connectivity Services [FF65+] ***/
pref("network.connectivity-service.enabled", false);
network.trr.custom_uri
- feel free to draft it up. I've already said that you'll have to expand on the description for "setting up" because, see earlier posts and discussions re for this to have effect (be used) it involves the other pref as well
- so this is all yours right now :trollface:
geo.provider.ms-windows-location (and the other ones for Mac, Linux, Droid)
- I think we should include them. IDK if it breaks anything. But I agree that the service used should be handled only within the application. So yeah, lets do it, active and disable them. Not sure how to word it - you do that shit for a living .. - so this is all yours right now :trollface: !!
edited to add trollfaces
About dom.targetBlankNoOpener.enabled.
It perform better (covers more) than addon Don't touch my tabs!.
Also doesn't create breakages... @earthlng extension covers a bit more (so its supperior), but it makes breakages in some web applications.
For sure Microsoft Web Exchange Control Panel suffers, where editing properties of some object is "spawn" into edit window and saving those changes does not update the main windows object.
Also found some more like upper example.
I would vote for dom.targetBlankNoOpener.enabled = true, at least until FF67+.
If someone needs complete solution, then still can use @earthlng extension as addition to this pref.
I would also not "touch" network.trr.uri and network.trr.custom_uri.
Its a user decision to use DoH or not. Some would like to avoid giving its DNS queries to ISP.
But, on the other hand, ISP can also track further on, due to DNS query is only a connection start, the connection to some domain anyway follows on some other protocol and destination can be tracked, despite the DNS query isn't revealed.
For sure using DoH might not be good for enterprise users.
Damn, I can't really decide by myselft whats better. :smile:
Love you all :heart:
Concerning dom.targetBlankNoOpener.enabled users of the _CanvasBlocker_ extension are protected as I understand it: CanvasBlocker also supports window.opener protection since v0.5.3-RC1. That's just for our information because, of course, a setting cannot depend on users' installed extension.
https://github.com/ghacksuserjs/ghacks-user.js/pull/637 - moved some stuff around and added a couple
dom.targetBlankNoOpener.enabledperform better (covers more) than addon Don't touch my tabs!
there are some differences, namely (1) the addon doesn't change links to the same domain whereas targetBlankNoOpener doesn't care about that and (2) targetBlankNoOpener also covers <area> elements instead of just <a> tags.
So yes I'd agree that targetBlankNoOpener is better than Don't touch my tabs! and makes that addon obsolete (unless you care about the "whitelisting" for same-domain)
CanvasBlocker uses essentially the same as my window.opener be gone! and is therefore pretty hardcore but comes with probably a bunch of breakage.
^^ targetBlankNoOpener allows devs to opt-out ie explicitly make links use rel=opener and IDK how Don't touch my tabs! deals with that. So that's potentially another difference between the 2.
They're also planning or already working on including protection for forms as well (<form> elements) and you don't need to install an extension so IMHO targetBlankNoOpener is pretty sweet for the average Joe.
If I can't do both of those, then fuck it
So you didn't add in the extension link .. fine, whateva ... over it .. I agree that some protection is better than none, that wasn't the only point. It was a chance to educate users: so many times I have seen people tout using don't touch my tabs or whateva that extension was, and AFAIK it's not good: false sense of security (for lack of a better word). But for some reason you are loath to promote your extension .. whateva .. over it .. your call.
howeva, good to know FF are expanding on the pref
earthlng commented 26 minutes ago ... I have about an hour to spare if you want to get this done now
am doing it ... I will finish it up if you're gone by the time I do finish it up (hope that makes no sense)
I don't care about promoting my extension 1 way or the other but if you want to mention an extension for this then it'd probably be better to recommend CanvasBlocker because it does the same thing and has other nice features as well. I didn't directly respond to your comments about this because it's such a mostly theoretical risk in the first place and is just not worth adding a lot of detailed and potentially confusing information to that pref. targetBlankNoOpener does a fine job and covers the most important risks; anything beyond that can be found by the more tech-savvy and interested parties quite easily, either in some of the comments on various issues here or in our wiki or anywhere else.
I mean adding a pref and then immediately point out that it's not perfect and recommending an extension that doesn't have any whitelisting capabilities and which can lead to a bunch of difficult to diagnose breakage just doesn't make a lot of sense IMO.
Thanks Pantski for finishing this. Last thing to do is create the release and I'll do the changelog
I knew I forgot something .. on it now
Most helpful comment
network.connectivity-service.*is really a bloated feature. All those checks should be done outside of a browser.