Ublock: Request to google-analytics.com is made, even if there is a block rule
Describe the issue
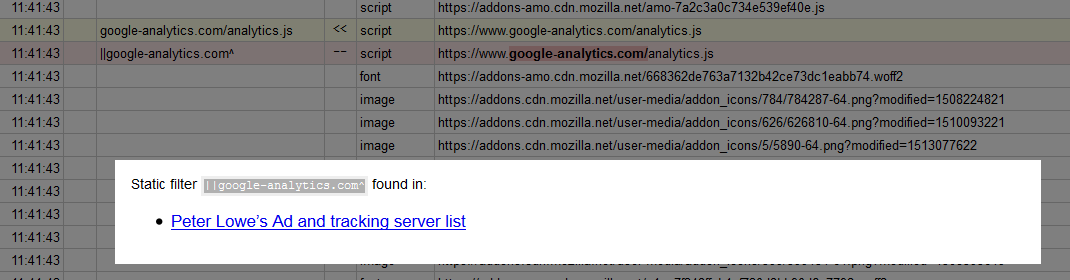
I have a block rule on google analytics as seen here:
the log shows that the request was blocked (as it should be), but looking in the ff developer tools network console, it looks like the request went to googles servers anyway:
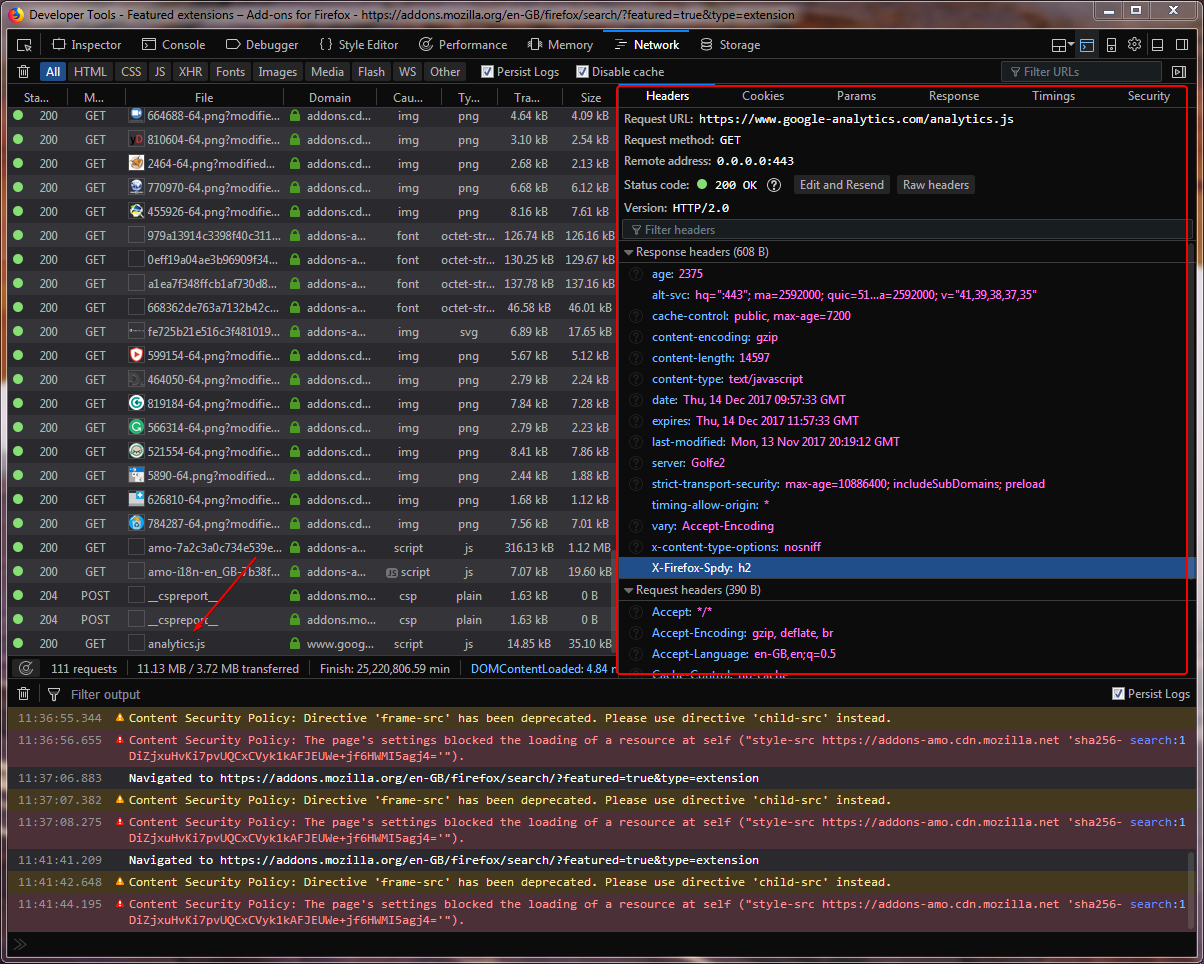
I read this and it says that requests should be blocked, so I looked at the proxy logs, and saw that the request traversed the proxy. So the request was definitely not blocked.
One or more specific URLs where the issue occurs
https://addons.mozilla.org/en-GB/firefox/search/?featured=true&type=extension
Steps for anyone to reproduce the issue
- go to https://addons.mozilla.org/en-GB/firefox/search/?featured=true&type=extension
- open the ublock origin logger on the page
- open wireshark/tcpdump and start a network trace
- refresh https://addons.mozilla.org/en-GB/firefox/search/?featured=true&type=extension
- look at the logger and confirm that the request to google-analytics is red - blocked
- look at the tcpdump/wireshark dump and observe that a request to a google ip was made
Your settings
add a block rule for
||google-analytics.com^
- OS/version: windows 7 64bit
- Browser/version: ff 57.0.2
- uBlock Origin version: 1.14.20
All 5 comments
Pages from addons.mozilla.org are privileged, WebExtensions extensions are not allowed to interfere on privileged pages.
Oh I did not know that. So mozilla can effectively disable adblock on their pages. Good to know, thanks and sorry for the spam.
Do you happen to know if this is this documented somewhere?
This has been talked a lot. I can't quickly find an official documentation for now from MDN.
https://www.reddit.com/r/firefox/comments/74i3nt/why_are_connections_to_googlecom_and_gstaticcom/
For FF57+ you can set privacy.resistFingerprinting.block_mozAddonManager-> true. Now AMO is no longer privileged. All this does is ignore three domains ( and seven other developer ones if another pref if flipped). See here . Ticket for reference is 1384330 - this has been built specifically for TBB.
Now, there was some talk about AMO now being open to script injection (you would need a malicious extension already installed) via service workers, which could possibly allow silent installations (of extensions). IDK about that .. and Mozilla thought nothing of it - see 1406795
To mitigate against this you can always just remove the special permissions - for reference type resource://app/defaults/permissions into your urlbar
user_pref("permissions.manager.defaultsUrl", "");
Additionally, google analytics are used on the get more addons panel - to get around this, blank the url that is looked up, and for good measure, hide the panel
user_pref("extensions.getAddons.showPane", false); // hidden pref
user_pref("extensions.webservice.discoverURL", "");
You can also choose not to use the system extension "Activity Stream" which is the whole revamped new tab thing - that too is privileged and no doubt uses analytics
user_pref("browser.newtabpage.activity-stream.enabled", false);
user_pref("browser.library.activity-stream.enabled", false); // (FF57+)
Thank you @Thorin-Oakenpants !
Most helpful comment
For FF57+ you can set
privacy.resistFingerprinting.block_mozAddonManager-> true. Now AMO is no longer privileged. All this does is ignore three domains ( and seven other developer ones if another pref if flipped). See here . Ticket for reference is 1384330 - this has been built specifically for TBB.Now, there was some talk about AMO now being open to script injection (you would need a malicious extension already installed) via service workers, which could possibly allow silent installations (of extensions). IDK about that .. and Mozilla thought nothing of it - see 1406795
To mitigate against this you can always just remove the special permissions - for reference type
resource://app/defaults/permissionsinto your urlbarAdditionally, google analytics are used on the get more addons panel - to get around this, blank the url that is looked up, and for good measure, hide the panel
You can also choose not to use the system extension "Activity Stream" which is the whole revamped new tab thing - that too is privileged and no doubt uses analytics