Shadowsocks-windows: 4.0.9突然无法访问,系统环境稳定
版本:4.0.9
操作环境:Win 7 x64 Version 6.1.7601 SP1 内部版本7601
操作步骤:直接运行
期望的结果:正常运行
实际结果:无错误提示,但是无法访问
配置文件和日志文件:
[2018-05-07 08:57:55] System.Reflection.TargetInvocationException: 操作过程中出现异常,结果无效。 有关异常的详细信息,请查看 InnerException。 ---> System.Net.WebException: 无法连接到远程服务器 ---> System.Net.Sockets.SocketException: 由于目标计算机积极拒绝,无法连接。 127.0.0.1:1080
在 System.Net.Sockets.Socket.EndConnect(IAsyncResult asyncResult)
在 System.Net.ServicePoint.ConnectSocketInternal(Boolean connectFailure, Socket s4, Socket s6, Socket& socket, IPAddress& address, ConnectSocketState state, IAsyncResult asyncResult, Exception& exception)
--- 内部异常堆栈跟踪的结尾 ---
在 System.Net.HttpWebRequest.EndGetResponse(IAsyncResult asyncResult)
在 System.Net.WebClient.GetWebResponse(WebRequest request, IAsyncResult result)
在 System.Net.WebClient.DownloadBitsResponseCallback(IAsyncResult result)
--- 内部异常堆栈跟踪的结尾 ---
在 System.ComponentModel.AsyncCompletedEventArgs.RaiseExceptionIfNecessary()
在 Shadowsocks.Controller.UpdateChecker.http_DownloadStringCompleted(Object sender, DownloadStringCompletedEventArgs e)
[2018-05-07 08:57:55] Shadowsocks started
[2018-05-07 08:57:56]
Registered Encryptor Info
aes-128-cfb=>StreamOpenSSLEncryptor
aes-192-cfb=>StreamOpenSSLEncryptor
aes-256-cfb=>StreamOpenSSLEncryptor
aes-128-ctr=>StreamOpenSSLEncryptor
aes-192-ctr=>StreamOpenSSLEncryptor
aes-256-ctr=>StreamOpenSSLEncryptor
bf-cfb=>StreamOpenSSLEncryptor
camellia-128-cfb=>StreamOpenSSLEncryptor
camellia-192-cfb=>StreamOpenSSLEncryptor
camellia-256-cfb=>StreamOpenSSLEncryptor
rc4-md5=>StreamOpenSSLEncryptor
salsa20=>StreamSodiumEncryptor
chacha20=>StreamSodiumEncryptor
chacha20-ietf=>StreamSodiumEncryptor
aes-128-gcm=>AEADOpenSSLEncryptor
aes-192-gcm=>AEADOpenSSLEncryptor
aes-256-gcm=>AEADOpenSSLEncryptor
chacha20-ietf-poly1305=>AEADOpenSSLEncryptor
xchacha20-ietf-poly1305=>AEADSodiumEncryptor
[2018-05-07 09:03:30] connect to mtalk.google.com:5228
[2018-05-07 09:03:30] connect to www.googleapis.com:443
[2018-05-07 09:03:31] Socket connected to ss server: 23.83.233.198:443
[2018-05-07 09:03:31] Socket connected to ss server: 23.83.233.198:443
[2018-05-07 09:03:31] connect to www.googleapis.com:443
[2018-05-07 09:03:31] connect to www.googleapis.com:443
[2018-05-07 09:03:31] Socket connected to ss server: 23.83.233.198:443
[2018-05-07 09:03:31] Socket connected to ss server: 23.83.233.198:443
[2018-05-07 09:03:32] connect to www.googleapis.com:443
[2018-05-07 09:03:32] Socket connected to ss server: 23.83.233.198:443
[2018-05-07 09:03:33] connect to www.googleapis.com:443
[2018-05-07 09:03:33] Socket connected to ss server: 23.83.233.198:443
[2018-05-07 09:03:34] connect to www.googleapis.com:443
[2018-05-07 09:03:34] connect to www.googleapis.com:443
[2018-05-07 09:03:34] Socket connected to ss server: 23.83.233.198:443
[2018-05-07 09:03:34] connect to s2.googleusercontent.com:443
[2018-05-07 09:03:34] connect to www.googleapis.com:443
[2018-05-07 09:03:35] Socket connected to ss server: 23.83.233.198:443
[2018-05-07 09:03:35] Socket connected to ss server: 23.83.233.198:443
[2018-05-07 09:03:35] connect to s2.googleusercontent.com:443
[2018-05-07 09:03:35] connect to s2.googleusercontent.com:443
[2018-05-07 09:03:35] connect to s2.googleusercontent.com:443
[2018-05-07 09:03:35] connect to s2.googleusercontent.com:443
[2018-05-07 09:03:35] connect to s2.googleusercontent.com:443
[2018-05-07 09:03:35] Socket connected to ss server: 23.83.233.198:443
[2018-05-07 09:03:35] Socket connected to ss server: 23.83.233.198:443
[2018-05-07 09:03:35] Socket connected to ss server: 23.83.233.198:443
[2018-05-07 09:03:35] Socket connected to ss server: 23.83.233.198:443
[2018-05-07 09:03:35] Socket connected to ss server: 23.83.233.198:443
[2018-05-07 09:03:35] connect to www.googleapis.com:443
[2018-05-07 09:03:35] Socket connected to ss server: 23.83.233.198:443
[2018-05-07 09:03:35] connect to ssl.google-analytics.com:443
[2018-05-07 09:03:35] Socket connected to ss server: 23.83.233.198:443
[2018-05-07 09:03:36] connect to www.googleapis.com:443
[2018-05-07 09:03:36] Socket connected to ss server: 23.83.233.198:443
[2018-05-07 09:03:37] connect to accounts.google.com:443
[2018-05-07 09:03:37] Socket connected to ss server: 23.83.233.198:443
[2018-05-07 09:03:38] connect to accounts.google.com:443
[2018-05-07 09:03:38] Socket connected to ss server: 23.83.233.198:443
[2018-05-07 09:03:39] 23.83.233.198:443 timed out
All 10 comments
你的BWG小鸡凉凉了啊
请双击屏幕右下角图标托盘区的SS纸飞机图标,找到右下角的 代理端口 并更换一个端口看看,比如更换成 2080 。
@GoogleGFW 并没有呢,我另一台笔记本连同样服务器是能用的,这个连不上的是公司台式机
@chenshaoju 刚刚试了一下,好像没木有效果诶
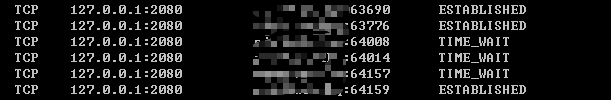
这个对troubleshooting有帮助吗?
有可能你公司的网络有屏蔽?
@chenshaoju 想问一下,我是能ping通的,即便这样也可能存在公司网络屏蔽吗?
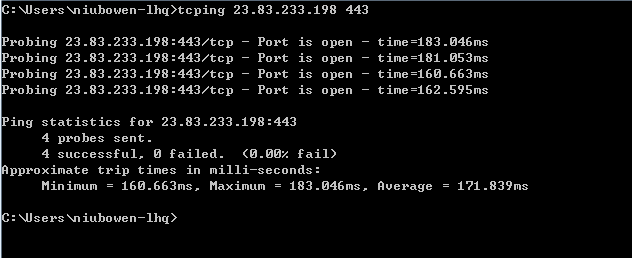
不一定,你可能需要使用 tcping 进行测试,你可以在 https://www.elifulkerson.com/projects/tcping.php 下载。
这是命令提示符应用,你需要在命令提示符(cmd)或PowerShell下执行,格式为:
tcping 123.45.67.89 9876
其中 123.45.67.89 替换为你的服务器IP, 9876 替换为你的你的SS端口,看看能否通?如果通,会提示 Port is open ,如果不通,会提示 No response 或 Port is close 。
还好不是公司发现我偷偷F|Q给我封了 罒ω罒
你所在的网络有WiFi吗?如果可能,可能需要测试一下手机上连上WiFi看看是否可用,或者需要在其他的计算机上测试一下。
如果手机4G可以,WiFi不行,很有可能是企业网有限制。
@chenshaoju 感谢您耐心解答,确实是公司网络限制,公司wifi也不行,访问google,结果那个白屏界面跟电脑访问一样,很好奇网管是怎么识别ss流量的
很多企业使用的安全产品都可以检出SS,比如深信服,但是仅仅是在网络传输过程中检出并屏蔽,你通过SS传输的内容目前是无法被破解的。
EDIT:
可参阅: https://twitter.com/HeyMe0w/status/833935038441889792
Most helpful comment
很多企业使用的安全产品都可以检出SS,比如深信服,但是仅仅是在网络传输过程中检出并屏蔽,你通过SS传输的内容目前是无法被破解的。
EDIT:
可参阅: https://twitter.com/HeyMe0w/status/833935038441889792