Serverless-application-model: Invalid resource for policy template: CodePipelineLambdaExecutionPolicy
Description:
Invalid resource for policy template: CodePipelineLambdaExecutionPolicy
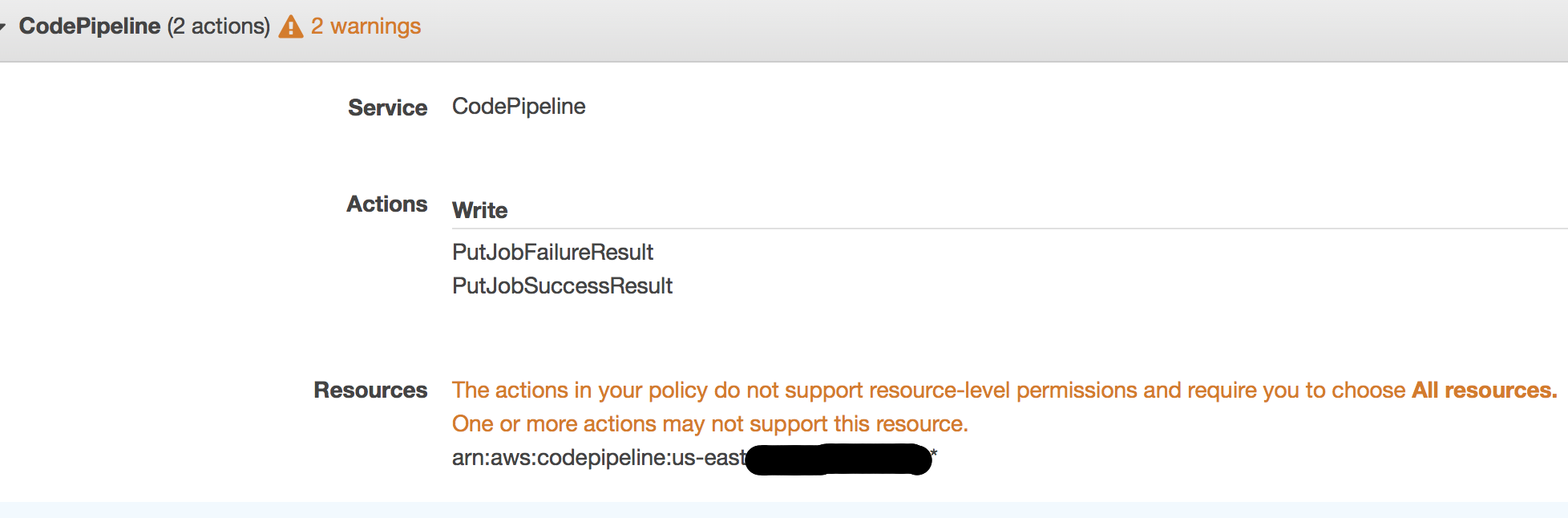
The codepipeline:PutJobSuccessResult and codepipeline:PutJobFailureResult actions require * for the resource in an IAM policy statement. The statement in the policy_templates.json is invalid:
Steps to reproduce the issue:
- Create a CFN template for a SAM
- Reference the policy template
CodePipelineLambdaExecutionPolicy: {} - Create the stack
- Try to access the lambda function from a pipeline action
Observed result:
Pipeline times out waiting for acknowledgement from lambda function because lambda function gets access denied error:
Aws::CodePipeline::Errors::AccessDeniedException: User: arn:aws:sts::0000000000:assumed-role/aws-serverless-repository-cfn/foo is not authorized to perform: codepipeline:PutJobFailureResult
Expected result:
Lambda should be able to acknowledge the pipeline.
All 5 comments
@sanathkr Any thoughts on this one? Would love to hear it is just me doing something wrong 😆
miss on our part. From their documentation: "You specify the actions in the policy's Action field, and you specify a wildcard character (*) as the resource value in the policy's Resource field. ". Fixing. Should update the issue on release. Apologies for the miss.
CodePipeline policy template was a nice addition. I can publish my app into Serverless Application Repository (only allows sam policy templates ) without having to add the IAM policy manually after deploying the app.
@salmanap don't forget us! 🙂I really don't mind fixing it by editing the IAM policy for my own use. It would be nice to have it fixed for apps published into AWS Application Repository to have it "plug & play" for other users.
Here is AWS policy editor complaining about the invalid Resources config in the policy.
Thanks!
@Tanbouz thanks for pinging. Do you want to submit a PR for this? It's simple to do via the GitHub UI (especially for Policy Template changes). I'll walk you through the steps:
- Open the file on the develop branch https://github.com/awslabs/serverless-application-model/blob/develop/samtranslator/policy_templates_data/policy_templates.json
- Click the pencil button next to the [Raw] [Blame] [History] buttons
- Scroll down to the
"CodePipelineLambdaExecutionPolicy"entry on line 824 - Replace the
"Resource"entry on line 837 with"Resource": "*" - Scroll to the bottom of the page and specify a commit message, e.g. "fix: fix Resource for CodePipelineLambdaExecutionPolicy policy template"
- In the text area below, write a more descriptive message summarizing the problem and link to this Issue; e.g. "The actions in this policy template require a "*" Resource as documented here https://docs.aws.amazon.com/codepipeline/latest/userguide/permissions-reference.html. closes #389"
- Click [Propose file change]
This will be fixed in our next release. Closing. Thanks again @Tanbouz