Rust-analyzer: cargo check output not showing up
After upgrading to 0.2.166 I no longer see cargo check output in the edit pane.
The extension now runs cargo check almost immediately after each edit (and not just upon save) which is good because that cargo check comes back quickly enough.
However, none of the errors, including clippy warnings, are showing up. They are just silently swallowed.
I have to manually run cargo check on the command line and manually Ctrl-Click each error position to get there. The errors are no longer red-underlined. I wonder what has happened.
All 38 comments
Did you enable auto save? The extension doesn't run cargo check automatically.
I used to, but then I turned it off. Now it only runs check after save. But still, the cargo check returns pretty fasts, much faster than if I run it manually.
But still nothing shows up in the edit pane.
Sorry, didn't mention I'm using VScode.
One data point: If I leave VScode sitting there for a while, suddenly all the clippy lints starts showing up. As if there is a huge delay.
There is this in the Rust Analyzer Language Server log:
error: expected one of `.`, `;`, `?`, `}`, or an operator, found `Ok`
--> <stdin>:37:5
|
36 | ))
| - expected one of `.`, `;`, `?`, `}`, or an operator
37 | Ok(())
| ^^ unexpected token
Hi all, I just tried to switch from rls tonight on a whim and I'm also not getting any error underlines in the latest version of rust-analyzer off the VSCode marketplace.
Downgraded to 0.2.159 and it works fine. So it is something to do with version 0.2.166
There is another anomaly: In 0.2.159, when clicking on Run Test, it only compiles the test file in question. In 0.2.166, when clicking on Run Test, it compiles all the test files.
Upgraded to 0.2.174 and unfortunately the problem still persists.
cargo check errors are not showing up.
Well, another version, and still the problem persists.
Since it doesn't seem anybody else in the world is screaming about this... I am beginning to think that maybe it has something to do with my installation of rust-analyzer...
I am seeing this in one of my projects. I get warnings about syntax errors and RA is adding all the type annotations, but any mistakes beyond syntax just don't show up. I assume this means cargo watch isn't running, though I can't see any obvious output that states one way or the other.
Downgrading to 0.2.159 fixes it for me.
It does seem to be project specific though - most of my projects work fine on the latest RA, just one of them that's suffering from this issue...
Downgrading to 0.2.159 fixes it for me.
Exactly. 0.2.159 is the last version that this works.
Can you share a project where this happens? Does cargo check --message-format=json emit the errors you expect?
Project I'm seeing this on is this one: https://github.com/polyandglot/cynic (and yes, cargo check works as expected when run directly)
It works for me, I suppose:

Can you share a project where this happens? Does
cargo check --message-format=jsonemit the errors you expect?
Yes, running cargo check in the terminal works fine. It is just not showing up in the edit panes are red swiggly lines.
It does seem to be project specific though - most of my projects work fine on the latest RA, just one of them that's suffering from this issue...
So far I checked three projects, two of them didn't work, one of them (one that I haven't touched for a while) works fine.
So I suppose it has something to do with some setting cached in vscode?
I tried making a clean clone of a project and still it doesn't work.
A rather heavy hammer would be to run strace -fp $(pidof rust-analyzer) or the equivalent, then trigger cargo check by running a file. strace will show whether it runs cargo check and what the latter emits.
It has this error:
ERR content modified: Error: content modified
at handleResponse (c:\Users\schun\.vscode\extensions\matklad.rust-analyzer-0.2.182\out\src\main.js:3531:48)
at processMessageQueue (c:\Users\schun\.vscode\extensions\matklad.rust-analyzer-0.2.182\out\src\main.js:3356:17)
at Immediate.<anonymous> (c:\Users\schun\.vscode\extensions\matklad.rust-analyzer-0.2.182\out\src\main.js:3340:13)
at processImmediate (internal/timers.js:439:21)
Does it help?
That's not really an error, it means that a LSP request was cancelled because you edited one of the files. I see it from time to time, but it's not necessarily related to your issue.
It works for me, I suppose:
@lnicola as I said, syntax errors appear fine. It's other errors I'm having issues with - like if I delete a struct & leave it's impls in place, rust analyzer is silent.
The behavior is that the cargo check, run after a save, complete very quickly. If run manually, it'll spit out a lot more errors, so I'm quite sure the cargo check has terminated prematurely or something.
For projects that work, the cargo check takes a reasonable amount of time.
@obmarg those were rustc errors. Here's a type checker one:

The behavior is that the cargo check, run after a save, complete very quickly. If run manually, it'll spit out a lot more errors, so I'm quite sure the cargo check has terminated prematurely or something.
I think cargo used to not re-emit warnings in incremental mode, so you would see no warnings on a second run. Errors would still be reported, though.What compiler version are you using, and do you have any special rust-analyzer settings like replacing cargo check with cargo clippy? Can you run strace as described above?
For projects that work, the cargo check takes a reasonable amount of time.
It should finish more or less instantly, at least on smaller projects:
--> cynic-querygen/src/type_index.rs:2:62
|
2 | use graphql_parser::schema::{Definition, Document, EnumType, ScalarType, TypeDefinition};
| ^^^^^^^^^^
|
= note: `#[warn(unused_imports)]` on by default
[snip]
warning: 18 warnings emitted
Checking cynic v0.1.2 (/home/me/cynic/cynic)
error[E0308]: mismatched types
--> cynic/src/lib.rs:243:24
|
243 | let foo: u32 = "bar";
| --- ^^^^^ expected `u32`, found `&str`
| |
| expected due to this
error: aborting due to previous error
For more information about this error, try `rustc --explain E0308`.
error: could not compile `cynic`.
To learn more, run the command again with --verbose.
cargo check 0.33s user 0.08s system 100% cpu 0.412 total
@obmarg I figured it out.
There happens to be a feature in my Cargo.toml that requires nightly, and my default toolchain is stable. This seems to be killing the cargo check. This seems to be the case even if the crate is pulled in only under a feature flag, as cargo check seems to be checking it also.
@lnicola Ah yeah - just tried this on another laptop and it's working as expected there, so definitely something local to this machine.
I'm running 1.42.0 of the compiler, not updated any rust-analyzer settings.
On macos so no strace, but used dtruss to do something similar. Not entirely sure how to intepret the output, but here it is:
dtrace: system integrity protection is on, some features will not be available
SYSCALL(args) = return
psynch_cvsignal(0x7FE2CF505A30, 0x11B0000011C00, 0x11B00) = 257 0
psynch_cvsignal(0x7FE2D1C57560, 0x1F0000002000, 0x1F00) = 257 0
psynch_mutexdrop(0x7FE2D1C28D00, 0x17400, 0x16600) = 0 0
pipe(0x0, 0x0, 0x0) = 3 0
ioctl(0x3, 0x20006601, 0x4) = 0 0
ioctl(0x4, 0x20006601, 0x0) = 0 0
pipe(0x0, 0x0, 0x0) = 5 0
ioctl(0x5, 0x20006601, 0x6) = 0 0
ioctl(0x6, 0x20006601, 0x0) = 0 0
posix_spawn(0x70001064B2F8, 0x70001064AE00, 0x70001064AA40) = -1 2
posix_spawn(0x70001064B2F8, 0x70001064AE00, 0x70001064AA40) = -1 2
posix_spawn(0x70001064B2F8, 0x70001064AE00, 0x70001064AA40) = -1 2
posix_spawn(0x70001064B2F8, 0x70001064AE00, 0x70001064AA40) = 0 0
stat64("/Users/graeme/.cargo/bin/rustfmt\0", 0x70001064AD30, 0x0) = 0 0
close_nocancel(0x3) = 0 0
close_nocancel(0x6) = 0 0
dtrace: error on enabled probe ID 2184 (ID 167: syscall::write:return): invalid kernel access in action #12 at DIF offset 68
close_nocancel(0x4) = 0 0
dtrace: error on enabled probe ID 2186 (ID 165: syscall::read:return): invalid kernel access in action #12 at DIF offset 68
dtrace: error on enabled probe ID 2186 (ID 165: syscall::read:return): invalid kernel access in action #12 at DIF offset 68
dtrace: error on enabled probe ID 2186 (ID 165: syscall::read:return): invalid kernel access in action #12 at DIF offset 68
dtrace: error on enabled probe ID 2186 (ID 165: syscall::read:return): invalid kernel access in action #12 at DIF offset 68
dtrace: error on enabled probe ID 2186 (ID 165: syscall::read:return): invalid kernel access in action #12 at DIF offset 68
dtrace: error on enabled probe ID 2186 (ID 165: syscall::read:return): invalid kernel access in action #12 at DIF offset 68
dtrace: error on enabled probe ID 2186 (ID 165: syscall::read:return): invalid kernel access in action #12 at DIF offset 68
dtrace: error on enabled probe ID 2186 (ID 165: syscall::read:return): invalid kernel access in action #12 at DIF offset 68
dtrace: error on enabled probe ID 2186 (ID 165: syscall::read:return): invalid kernel access in action #12 at DIF offset 68
close_nocancel(0x5) = 0 0
wait4(0xE14E, 0x70001064B2C8, 0x0) = 57678 0
psynch_cvsignal(0x7FE2CF505A30, 0x11C0000011D00, 0x11C00) = 257 0
psynch_cvwait(0x7FE2CF505A30, 0x11C0100011D00, 0x11C00) = 0 0
psynch_cvsignal(0x7FE2CF506CF0, 0xBC000000BD00, 0xBC00) = 257 0
dtrace: error on enabled probe ID 2184 (ID 167: syscall::write:return): invalid kernel access in action #12 at DIF offset 68
dtrace: error on enabled probe ID 2184 (ID 167: syscall::write:return): invalid kernel access in action #12 at DIF offset 68
dtrace: error on enabled probe ID 2186 (ID 165: syscall::read:return): invalid kernel access in action #12 at DIF offset 68
psynch_cvsignal(0x7FE2CF505A30, 0x11D0000011E00, 0x11D00) = 257 0
psynch_cvwait(0x7FE2CF505A30, 0x11D0100011E00, 0x11D00) = 0 0
psynch_cvsignal(0x7FE2D1C6BD50, 0x80000000900, 0x800) = 257 0
psynch_cvsignal(0x7FE2CF505A30, 0x11E0000011F00, 0x11E00) = 257 0
psynch_cvwait(0x7FE2CF505A30, 0x11E0100011F00, 0x11E00) = 0 0
stat64("/Users/graeme/.pyenv/shims/cargo\0", 0x700010244E70, 0x0) = -1 2
stat64("/Users/graeme/.asdf/shims/cargo\0", 0x700010244E70, 0x0) = -1 2
stat64("/Users/graeme/.asdf/bin/cargo\0", 0x700010244E70, 0x0) = -1 2
stat64("/Users/graeme/.cargo/bin/cargo\0", 0x700010244E70, 0x0) = 0 0
bsdthread_create(0x10B9F2D00, 0x7FE2CF4A9960, 0x7000144A9000) = 340430848 0
thread_selfid(0x0, 0x0, 0x0) = 6557144 0
sigaltstack(0x0, 0x7000144A8F80, 0x0) = 0 0
mmap(0x0, 0x20000, 0x3, 0x1002, 0xFFFFFFFFFFFFFFFF, 0x0) = 0x111AA0000 0
sigaltstack(0x7000144A8F80, 0x0, 0x0) = 0 0
psynch_cvsignal(0x7FE2D1C6BD50, 0x90000000A00, 0x900) = 257 0
psynch_cvwait(0x7FE2D1C6BD50, 0x90100000A00, 0x900) = 0 0
psynch_cvsignal(0x7FE2CF505A30, 0x11F0000012000, 0x11F00) = 257 0
open("/dev/null\0", 0x1000000, 0x1B6) = 3 0
psynch_cvwait(0x7FE2CF505A30, 0x11F0100012000, 0x11F00) = 0 0
pipe(0x0, 0x0, 0x0) = 4 0
ioctl(0x4, 0x20006601, 0x5) = 0 0
ioctl(0x5, 0x20006601, 0x0) = 0 0
psynch_cvsignal(0x7FE2CF506CF0, 0xBD000000BE00, 0xBD00) = 257 0
psynch_cvwait(0x7FE2CF506CF0, 0xBD010000BE00, 0xBD00) = 0 0
open("/dev/null\0", 0x1000001, 0x1B6) = 6 0
dtrace: error on enabled probe ID 2184 (ID 167: syscall::write:return): invalid kernel access in action #12 at DIF offset 68
dtrace: error on enabled probe ID 2184 (ID 167: syscall::write:return): invalid kernel access in action #12 at DIF offset 68
posix_spawn(0x7000144A82A8, 0x7000144A7DB0, 0x7000144A79F0) = -1 2
posix_spawn(0x7000144A82A8, 0x7000144A7DB0, 0x7000144A79F0) = -1 2
posix_spawn(0x7000144A82A8, 0x7000144A7DB0, 0x7000144A79F0) = -1 2
posix_spawn(0x7000144A82A8, 0x7000144A7DB0, 0x7000144A79F0) = 0 0
stat64("/Users/graeme/.cargo/bin/cargo\0", 0x7000144A7CE0, 0x0) = 0 0
close_nocancel(0x3) = 0 0
close_nocancel(0x5) = 0 0
close_nocancel(0x6) = 0 0
dtrace: error on enabled probe ID 2186 (ID 165: syscall::read:return): invalid kernel access in action #12 at DIF offset 68
dtrace: error on enabled probe ID 2186 (ID 165: syscall::read:return): invalid kernel access in action #12 at DIF offset 68
dtrace: error on enabled probe ID 2186 (ID 165: syscall::read:return): invalid kernel access in action #12 at DIF offset 68
dtrace: error on enabled probe ID 2186 (ID 165: syscall::read:return): invalid kernel access in action #12 at DIF offset 68
dtrace: error on enabled probe ID 2186 (ID 165: syscall::read:return): invalid kernel access in action #12 at DIF offset 68
dtrace: error on enabled probe ID 2186 (ID 165: syscall::read:return): invalid kernel access in action #12 at DIF offset 68
dtrace: error on enabled probe ID 2186 (ID 165: syscall::read:return): invalid kernel access in action #12 at DIF offset 68
dtrace: error on enabled probe ID 2186 (ID 165: syscall::read:return): invalid kernel access in action #12 at DIF offset 68
close_nocancel(0x4) = 0 0
kill(57682, 9) = 0 0
wait4(0xE152, 0x7000144A8368, 0x0) = 57682 0
psynch_cvsignal(0x7FE2D1C6BD50, 0xA0000000B00, 0xA00) = 257 0
sigaltstack(0x7000144A8F80, 0x0, 0x0) = 0 0
munmap(0x111AA0000, 0x20000) = 0 0
__disable_threadsignal(0x1, 0x0, 0x0) = 0 0
psynch_cvwait(0x7FE2D1C6BD50, 0xA0100000B00, 0xA00) = 0 0
psynch_cvsignal(0x7FE2CF505A30, 0x1200000012100, 0x12000) = 257 0
psynch_cvwait(0x7FE2CF505A30, 0x1200100012100, 0x12000) = 0 0
psynch_cvsignal(0x7FE2CF506CF0, 0xBE000000BF00, 0xBE00) = 257 0
psynch_cvwait(0x7FE2CF506CF0, 0xBE010000BF00, 0xBE00) = 0 0
dtrace: error on enabled probe ID 2184 (ID 167: syscall::write:return): invalid kernel access in action #12 at DIF offset 68
dtrace: error on enabled probe ID 2184 (ID 167: syscall::write:return): invalid kernel access in action #12 at DIF offset 68
dtrace: error on enabled probe ID 2186 (ID 165: syscall::read:return): invalid kernel access in action #12 at DIF offset 68
psynch_cvsignal(0x7FE2CF505A30, 0x1210000012200, 0x12100) = 257 0
psynch_cvwait(0x7FE2CF505A30, 0x1210100012200, 0x12100) = 0 0
psynch_cvsignal(0x7FE2D1844EC0, 0x20000000300, 0x200) = 257 0
stat64("/Users/graeme/src/cynic/cynic-codegen/src/query_dsl/argument_struct.rs\0", 0x700010042680, 0x0) = 0 0
open("/Users/graeme/src/cynic/cynic-codegen/src/query_dsl/argument_struct.rs\0", 0x1000000, 0x1B6) = 3 0
fstat64(0x3, 0x700010042640, 0x0) = 0 0
dtrace: error on enabled probe ID 2186 (ID 165: syscall::read:return): invalid kernel access in action #12 at DIF offset 68
dtrace: error on enabled probe ID 2186 (ID 165: syscall::read:return): invalid kernel access in action #12 at DIF offset 68
close_nocancel(0x3) = 0 0
psynch_cvsignal(0x7FE2CF505A30, 0x1220000012300, 0x12200) = 257 0
psynch_cvwait(0x7FE2CF505A30, 0x1220100012300, 0x12200) = 0 0
There happens to be a feature in my Cargo.toml that requires nightly
By default rust-analyzer passes --all-features to cargo check. You can use "rust-analyzer.cargo.allFeatures": false to prevent this.
@obmarg that log seems truncated. Did you use dtruss -f to follow the child processes? Otherwise I don't know much about MacOS.
@lnicola ah yeah, I know very little about dtruss so didn't realise that was an option 🤦
If i run dtruss -p 57898 -f I get this:
dtrace: system integrity protection is on, some features will not be available
PID/THRD SYSCALL(args) = return
57898/0x6427ba: psynch_cvsignal(0x7FA9B94095A0, 0x2620000026300, 0x26200) = 257 0
57898/0x6427b6: psynch_cvsignal(0x7FA9B954D280, 0x1E0000001F00, 0x1E00) = 257 0
57898/0x642a63: psynch_mutexdrop(0x7FA9B954CF10, 0x1C000, 0x1B200) = 0 0
57898/0x642a63: psynch_cvsignal(0x7FA9B94095A0, 0x2630000026400, 0x26300) = 257 0
57898/0x6427b6: psynch_cvwait(0x7FA9B94095A0, 0x2630100026400, 0x26300) = 0 0
57898/0x6427b6: psynch_cvsignal(0x7FA9B940A7B0, 0x16D0000016E00, 0x16D00) = 257 0
dtrace: error on enabled probe ID 2184 (ID 167: syscall::write:return): invalid kernel access in action #13 at DIF offset 68
dtrace: error on enabled probe ID 2184 (ID 167: syscall::write:return): invalid kernel access in action #13 at DIF offset 68
dtrace: error on enabled probe ID 2186 (ID 165: syscall::read:return): invalid kernel access in action #13 at DIF offset 68
57898/0x6427ba: psynch_cvsignal(0x7FA9B94095A0, 0x2640000026500, 0x26400) = 257 0
57898/0x6427b6: psynch_cvwait(0x7FA9B94095A0, 0x2640100026500, 0x26400) = 0 0
57898/0x6427b6: psynch_cvsignal(0x7FA9B954D0A0, 0x160000001700, 0x1600) = 257 0
57898/0x642a61: psynch_cvwait(0x7FA9B954D0A0, 0x160100001700, 0x1600) = 0 0
57898/0x642a61: psynch_mutexdrop(0x7FA9B954CF10, 0x1C100, 0x1B300) = 0 0
57898/0x642a61: pipe(0x0, 0x0, 0x0) = 3 0
57898/0x642a61: ioctl(0x3, 0x20006601, 0x4) = 0 0
57898/0x642a61: ioctl(0x4, 0x20006601, 0x0) = 0 0
57898/0x642a61: pipe(0x0, 0x0, 0x0) = 5 0
57898/0x642a61: ioctl(0x5, 0x20006601, 0x6) = 0 0
57898/0x642a61: ioctl(0x6, 0x20006601, 0x0) = 0 0
57898/0x642a61: posix_spawn(0x700004F542F8, 0x700004F53E00, 0x700004F53A40) = -1 2
57898/0x642a61: posix_spawn(0x700004F542F8, 0x700004F53E00, 0x700004F53A40) = -1 2
57898/0x642a61: posix_spawn(0x700004F542F8, 0x700004F53E00, 0x700004F53A40) = -1 2
57898/0x642a61: posix_spawn(0x700004F542F8, 0x700004F53E00, 0x700004F53A40) = 0 0
57898/0x642a61: stat64("/Users/graeme/.cargo/bin/rustfmt\0", 0x700004F53D30, 0x0) = 0 0
57898/0x642a61: close_nocancel(0x3) = 0 0
57898/0x642a61: close_nocancel(0x6) = 0 0
dtrace: error on enabled probe ID 2184 (ID 167: syscall::write:return): invalid kernel access in action #13 at DIF offset 68
57898/0x642a61: close_nocancel(0x4) = 0 0
dtrace: error on enabled probe ID 2186 (ID 165: syscall::read:return): invalid kernel access in action #13 at DIF offset 68
dtrace: error on enabled probe ID 2186 (ID 165: syscall::read:return): invalid kernel access in action #13 at DIF offset 68
dtrace: error on enabled probe ID 2186 (ID 165: syscall::read:return): invalid kernel access in action #13 at DIF offset 68
dtrace: error on enabled probe ID 2186 (ID 165: syscall::read:return): invalid kernel access in action #13 at DIF offset 68
dtrace: error on enabled probe ID 2186 (ID 165: syscall::read:return): invalid kernel access in action #13 at DIF offset 68
dtrace: error on enabled probe ID 2186 (ID 165: syscall::read:return): invalid kernel access in action #13 at DIF offset 68
dtrace: error on enabled probe ID 2186 (ID 165: syscall::read:return): invalid kernel access in action #13 at DIF offset 68
dtrace: error on enabled probe ID 2186 (ID 165: syscall::read:return): invalid kernel access in action #13 at DIF offset 68
dtrace: error on enabled probe ID 2186 (ID 165: syscall::read:return): invalid kernel access in action #13 at DIF offset 68
57898/0x642a61: close_nocancel(0x5) = 0 0
57898/0x642a61: wait4(0xE345, 0x700004F542C8, 0x0) = 58181 0
57898/0x642a61: psynch_cvsignal(0x7FA9B94095A0, 0x2650000026600, 0x26500) = 257 0
57898/0x6427b6: psynch_cvwait(0x7FA9B94095A0, 0x2650100026600, 0x26500) = 0 0
57898/0x6427b6: psynch_cvsignal(0x7FA9B940A7B0, 0x16E0000016F00, 0x16E00) = 257 0
57898/0x6427b9: psynch_cvwait(0x7FA9B940A7B0, 0x16E0100016F00, 0x16E00) = 0 0
dtrace: error on enabled probe ID 2184 (ID 167: syscall::write:return): invalid kernel access in action #13 at DIF offset 68
dtrace: error on enabled probe ID 2184 (ID 167: syscall::write:return): invalid kernel access in action #13 at DIF offset 68
dtrace: error on enabled probe ID 2186 (ID 165: syscall::read:return): invalid kernel access in action #13 at DIF offset 68
57898/0x6427ba: psynch_cvsignal(0x7FA9B94095A0, 0x2660000026700, 0x26600) = 257 0
57898/0x6427b6: psynch_cvwait(0x7FA9B94095A0, 0x2660100026700, 0x26600) = 0 0
57898/0x6427b6: psynch_cvsignal(0x7FA9B9544160, 0x70000000800, 0x700) = 257 0
57898/0x642a60: stat64("/Users/graeme/.pyenv/shims/cargo\0", 0x700004D50E70, 0x0) = -1 2
57898/0x642a60: stat64("/Users/graeme/.asdf/shims/cargo\0", 0x700004D50E70, 0x0) = -1 2
57898/0x642a60: stat64("/Users/graeme/.asdf/bin/cargo\0", 0x700004D50E70, 0x0) = -1 2
57898/0x642a60: stat64("/Users/graeme/.cargo/bin/cargo\0", 0x700004D50E70, 0x0) = 0 0
57898/0x642a60: bsdthread_create(0x107C43D00, 0x7FA9AD0FC7B0, 0x700008FB5000) = 150687744 0
57898/0x643915: thread_selfid(0x0, 0x0, 0x0) = 6568213 0
57898/0x643915: sigaltstack(0x0, 0x700008FB4F80, 0x0) = 0 0
57898/0x643915: mmap(0x0, 0x20000, 0x3, 0x1002, 0xFFFFFFFFFFFFFFFF, 0x0) = 0x10DA73000 0
57898/0x643915: sigaltstack(0x700008FB4F80, 0x0, 0x0) = 0 0
57898/0x643915: psynch_cvsignal(0x7FA9B9544160, 0x80000000900, 0x800) = 257 0
57898/0x642a60: psynch_cvwait(0x7FA9B9544160, 0x80100000900, 0x800) = 0 0
57898/0x642a60: psynch_cvsignal(0x7FA9B94095A0, 0x2670000026800, 0x26700) = 257 0
57898/0x6427b6: psynch_cvwait(0x7FA9B94095A0, 0x2670100026800, 0x26700) = 0 0
57898/0x643915: open("/dev/null\0", 0x1000000, 0x1B6) = 3 0
57898/0x643915: pipe(0x0, 0x0, 0x0) = 4 0
57898/0x643915: ioctl(0x4, 0x20006601, 0x5) = 0 0
57898/0x6427b6: psynch_cvsignal(0x7FA9B940A7B0, 0x16F0000017000, 0x16F00) = 257 0
57898/0x643915: ioctl(0x5, 0x20006601, 0x0) = 0 0
57898/0x6427b9: psynch_cvwait(0x7FA9B940A7B0, 0x16F0100017000, 0x16F00) = 0 0
57898/0x643915: open("/dev/null\0", 0x1000001, 0x1B6) = 6 0
dtrace: error on enabled probe ID 2184 (ID 167: syscall::write:return): invalid kernel access in action #13 at DIF offset 68
dtrace: error on enabled probe ID 2184 (ID 167: syscall::write:return): invalid kernel access in action #13 at DIF offset 68
57898/0x643915: posix_spawn(0x700008FB42A8, 0x700008FB3DB0, 0x700008FB39F0) = -1 2
57898/0x643915: posix_spawn(0x700008FB42A8, 0x700008FB3DB0, 0x700008FB39F0) = -1 2
57898/0x643915: posix_spawn(0x700008FB42A8, 0x700008FB3DB0, 0x700008FB39F0) = -1 2
57898/0x643915: posix_spawn(0x700008FB42A8, 0x700008FB3DB0, 0x700008FB39F0) = 0 0
57898/0x643915: stat64("/Users/graeme/.cargo/bin/cargo\0", 0x700008FB3CE0, 0x0) = 0 0
57898/0x643915: close_nocancel(0x3) = 0 0
57898/0x643915: close_nocancel(0x5) = 0 0
57898/0x643915: close_nocancel(0x6) = 0 0
dtrace: error on enabled probe ID 2186 (ID 165: syscall::read:return): invalid kernel access in action #13 at DIF offset 68
dtrace: error on enabled probe ID 2186 (ID 165: syscall::read:return): invalid kernel access in action #13 at DIF offset 68
dtrace: error on enabled probe ID 2186 (ID 165: syscall::read:return): invalid kernel access in action #13 at DIF offset 68
dtrace: error on enabled probe ID 2186 (ID 165: syscall::read:return): invalid kernel access in action #13 at DIF offset 68
dtrace: error on enabled probe ID 2186 (ID 165: syscall::read:return): invalid kernel access in action #13 at DIF offset 68
dtrace: error on enabled probe ID 2186 (ID 165: syscall::read:return): invalid kernel access in action #13 at DIF offset 68
dtrace: error on enabled probe ID 2186 (ID 165: syscall::read:return): invalid kernel access in action #13 at DIF offset 68
dtrace: error on enabled probe ID 2186 (ID 165: syscall::read:return): invalid kernel access in action #13 at DIF offset 68
57898/0x643915: close_nocancel(0x4) = 0 0
57898/0x643915: kill(58185, 9) = 0 0
57898/0x643915: wait4(0xE349, 0x700008FB4368, 0x0) = 58185 0
57898/0x643915: psynch_cvsignal(0x7FA9B9544160, 0x90000000A00, 0x900) = 257 0
57898/0x642a60: psynch_cvwait(0x7FA9B9544160, 0x90100000A00, 0x900) = 0 0
57898/0x643915: sigaltstack(0x700008FB4F80, 0x0, 0x0) = 0 0
57898/0x643915: munmap(0x10DA73000, 0x20000) = 0 0
57898/0x643915: __disable_threadsignal(0x1, 0x0, 0x0) = 0 0
57898/0x642a60: psynch_cvsignal(0x7FA9B94095A0, 0x2680000026900, 0x26800) = 257 0
57898/0x6427b6: psynch_cvwait(0x7FA9B94095A0, 0x2680100026900, 0x26800) = 0 0
57898/0x6427b6: psynch_cvsignal(0x7FA9B940A7B0, 0x1700000017100, 0x17000) = 257 0
57898/0x6427b9: psynch_cvwait(0x7FA9B940A7B0, 0x1700100017100, 0x17000) = 0 0
dtrace: error on enabled probe ID 2184 (ID 167: syscall::write:return): invalid kernel access in action #13 at DIF offset 68
dtrace: error on enabled probe ID 2184 (ID 167: syscall::write:return): invalid kernel access in action #13 at DIF offset 68
dtrace: error on enabled probe ID 2186 (ID 165: syscall::read:return): invalid kernel access in action #13 at DIF offset 68
dtrace: error on enabled probe ID 2186 (ID 165: syscall::read:return): invalid kernel access in action #13 at DIF offset 68
57898/0x6427ba: psynch_cvsignal(0x7FA9B94095A0, 0x2690000026A00, 0x26900) = 257 0
57898/0x6427b6: psynch_cvwait(0x7FA9B94095A0, 0x2690100026A00, 0x26900) = 0 0
57898/0x6427b6: psynch_cvsignal(0x7FA9BBA099F0, 0x10000000200, 0x100) = 257 0
57898/0x642a56: stat64("/Users/graeme/src/cynic/cynic/src/argument.rs\0", 0x700004B4E680, 0x0) = 0 0
57898/0x642a56: open("/Users/graeme/src/cynic/cynic/src/argument.rs\0", 0x1000000, 0x1B6) = 3 0
57898/0x642a56: fstat64(0x3, 0x700004B4E640, 0x0) = 0 0
dtrace: error on enabled probe ID 2186 (ID 165: syscall::read:return): invalid kernel access in action #13 at DIF offset 68
dtrace: error on enabled probe ID 2186 (ID 165: syscall::read:return): invalid kernel access in action #13 at DIF offset 68
57898/0x642a56: close_nocancel(0x3) = 0 0
57898/0x642a56: psynch_cvsignal(0x7FA9B94095A0, 0x26A0000026B00, 0x26A00) = 257 0
57898/0x6427b6: psynch_cvwait(0x7FA9B94095A0, 0x26A0100026B00, 0x26A00) = 0 0
dtrace: error on enabled probe ID 2186 (ID 165: syscall::read:return): invalid kernel access in action #13 at DIF offset 68
57898/0x6427ba: psynch_cvsignal(0x7FA9B94095A0, 0x26B0000026C00, 0x26B00) = 257 0
57898/0x6427b6: psynch_cvwait(0x7FA9B94095A0, 0x26B0100026C00, 0x26B00) = 0 0
57898/0x6427b6: psynch_cvsignal(0x7FA9BBA099F0, 0x20000000300, 0x200) = 257 0
57898/0x642a56: psynch_cvwait(0x7FA9BBA099F0, 0x20100000300, 0x200) = 0 0
57898/0x642a56: stat64("/Users/graeme/src/cynic/cynic/src/argument.rs\0", 0x700004B4E680, 0x0) = 0 0
57898/0x642a56: open("/Users/graeme/src/cynic/cynic/src/argument.rs\0", 0x1000000, 0x1B6) = 3 0
57898/0x642a56: fstat64(0x3, 0x700004B4E640, 0x0) = 0 0
dtrace: error on enabled probe ID 2186 (ID 165: syscall::read:return): invalid kernel access in action #13 at DIF offset 68
dtrace: error on enabled probe ID 2186 (ID 165: syscall::read:return): invalid kernel access in action #13 at DIF offset 68
57898/0x642a56: close_nocancel(0x3) = 0 0
57898/0x642a56: psynch_cvsignal(0x7FA9B94095A0, 0x26C0000026D00, 0x26C00) = 257 0
57898/0x6427b6: psynch_cvwait(0x7FA9B94095A0, 0x26C0100026D00, 0x26C00) = 0 0
Not sure if I'm misinterpreting, but the fact that there's only one PID output suggests to me it's not spawning a child process? I could be doing something wrong though, I've never used dtruss prior to this...
cargo check seems to be running with _all features enabled_. In my case, one of the features require nightly, and so that blows up the whole thing.
Strange there is simply no way to turn off this cargo check with all features enabled, short of removing all features.
Now, removing all features, but if that crate still resides in dependencies it'll also blow up. Therefore, the only way to get around it is to also remove that dependency.
@schungx doesn't "rust-analyzer.checkOnSave.allFeatures": false disable that?
@schungx doesn't
"rust-analyzer.checkOnSave.allFeatures": falsedisable that?
That's the point. It is _supposed_ to, but I'm now _quite_ sure that cargo check --all-features is called regardless. There is no way to turn it off.
@obmarg It does spawn a child process, but dtruss doesn't trace it because MacOS (or so I assume).
57898/0x643915: stat64("/Users/graeme/.cargo/bin/cargo\0", 0x700008FB3CE0, 0x0) = 0 0
[...]
57898/0x643915: kill(58185, 9) = 0 0
57898/0x643915: wait4(0xE349, 0x700008FB4368, 0x0) = 58185 0
That looks like this function. What do you get for cargo check --all-features --message-format=json?
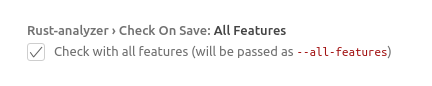
@schungx Just to make sure, if you disabled this:
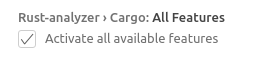
that's not the setting you're looking for. You want this:
@lnicola Yeah, does look a lot like that function. If I pipe that command out to a file i get this (200kb, so didn't want to put it inline):
If I pipe that command out to a file i get this
That looks all right (the warnings are there, at least), so I'm not sure what's up.
Yeah, it's an odd one. Guess for now I can use an older version of RA (or my other computer).
Might try and debug it myself if I get some time later, though got a ton of other stuff to do. Thanks for the help anyway.
@lnicola you're right.
Rust-analyzer > Check On Save: All Features
Turn it OFF (it defaults to true).
I think this option is newly added.
Two options with similar names is gotta create some confusion...
OK, closing this. I think I know what happens.
cargo check on save will stop when it encounters serious errors (in my case, accidentally turning on no-std build due to the default option Rust-analyzer > Check On Save: All Features), and if it dies early enough before other error output, then the edit panes will simply show nothing.
The trick is to notice that cargo check upon save completes extremely fast, and maybe an error in the log pane. Normally cargo check will run for some seconds for reasonably-sized projects.
Rust Analyzer does not detect that cargo check has terminated abnormally. It just merrily shows the only error message and stops.
By default rust-analyzer passes
--all-featurestocargo check. You can use"rust-analyzer.cargo.allFeatures": falseto prevent this.
That's not the correct one. It is another option Rust-analyzer > Check On Save: All Features which is rust-analyzer.checkOnSave.allFeatures instead.
@obmarg since schungx closed this issue and yours seems to be unrelated, can you please file a new one with the relevant details (repository URL, screenshots and so on)?
Oops, sorry! Reopen