Passport: Return access_token if token_id existed instead of creating new one
Used the Password Grant Tokens (version 2.0.10), everything works perfectly.
But when I looked at the database, I found that in table oauth_access_tokens, it creates new token id if user re-login (with same user_id, client_id, scopes), something likes:

Part of code is
$request->request->add([
'username' => $request->email,
'password' => $request->password,
'grant_type' => 'password',
'client_id' => $client->id,
'client_secret' => $client->secret,
'scope' => '*'
]);
$proxy = Request::create('oauth/token', 'POST');
$proxy_response = Route::dispatch($proxy);
client_id and client_secret are obtained from table oauth_clients.
My question is that, how can directly return access_token if it already existed instead of creating the new token id in table oauth_access_tokens?
PS: I knew I can obtain token_id by using $user->tokens, but how can I get access_token, refresh_token through token_id? (Maybe I miss something in doc)
Thanks a lot.
All 7 comments
I have similar question. Maybe we miss something from the flow
This is correct behaviour for OAuth - a new request for an OAuth token results in a new access token
@alexbilbie Thank you so much for your reply.
I understand what you said, but I'm afraid that, in database, it maybe have many redundant data in table oauth_access_tokens.
So I would like to know, does it hava any solution to directly generate access_token and refresh_token by using token_id in table oauth_access_tokens instead of creating new record?
Thanks
In the mean time in my case I did stored the token in the local storage of the ionic2 app I am developing, and I only refresh it when / before is expiring
@malutanpetronel Thanks for your suggestion.
But how about that if user logout, and re-login? Do you need remove the toke in LocalStorage and resend a request to fetch access_token?
The solution to the redundant data is to write a Console scheduled job to run every day and remove old access tokens
:+1: also confused by the documentation on this. it gives a pathway for creating an access token after creating the client, but if you logout (with session clear) and in again, it creates new access tokens for each login. So the OAuth status page ends up with an _Authorized Application_ for each login, which doesn't make sense.
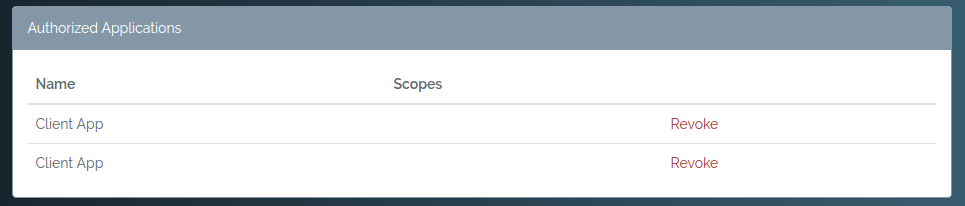
Should the logout process revoke the existing token instead? That's a bit drastic for a logout. I have given permission already, I don't want to do that again, I just want to logout. Logging in again should re-use the existing access_token.
Most helpful comment
The solution to the redundant data is to write a Console scheduled job to run every day and remove old access tokens