Community: Set default org-level project board permissions
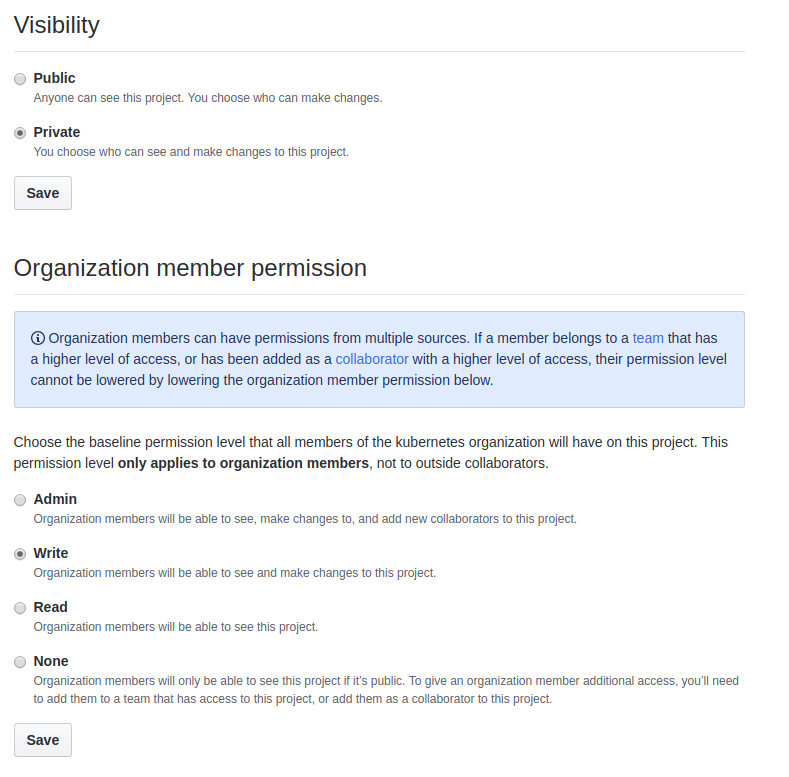
In discussing project grooming, I noticed that the default visibility for org-level project boards are private and default permissions are write. Ideally, these would be public and ~read~ write.
I checked on my own org and there doesn't seem to be a way to set defaults for project boards.
Is this something we can maybe enforce for each board via peribolos?
/sig pm
/area peribolos
All 16 comments
/area github-management
Is this something we can maybe enforce for each board via peribolos?
It's not possible today but I think it should be possible to add a feature for this: https://developer.github.com/v3/projects/#update-a-project.
/cc @cblecker @fejta
For now, if there is consensus, we can flip the settings for all boards so that they are Public and org members have Read access.
@nikhita -- I'm in favor of that.
Can you list the project board admins for org-level projects here so we can get their approval? I don't believe I have the rights to do that myself.
Private + Write:
- 1.14 CI Signal - @mariantalla
- SIG NETWORK - @bowei
Public + Read:
- SIG PM - @justaugustus + kubernetes/project-board-maintainers@
- API reviews - @liggitt + kubernetes/api-approvers@ + kubernetes/api-reviewers@
- Cloud Provider Azure - @justaugustus + @PatrickLang + kubernetes/sig-azure@
- KEP Implementation tracking - @justaugustus + kubernetes/kep-maintainers@ + kubernetes/project-board-maintainers@
- Contributor Experience - @calebamiles + kubernetes/community-admins@ + kubernetes/community-maintainers@
Public + Write:
- cncf-k8s-conformance-wg - @spiffxp + kubernetes/cncf-conformance-wg@
- SIG-Windows - @PatrickLang
- Deflaking kubernetes e2e tests - @mariantalla
- WG LTS - @justaugustus
- Kubernetes Infrastructure Team - @dims and @cblecker
I'm more of a fan of Write being the default, because it means contributors can move and add cards themselves. Please leave as such for the cncf-k8s-conformance-wg board, and I would prefer the same for the Deflaking board.
+1 to write being the default. We want members to be able to update the SIG-Windows board on their own as they take work items. It's good having this board in the org instead of a separate Trello because it's discoverable and doesn't require separate permissions.
@spiffxp / @PatrickLang -- Right you are; just looked over the permissions again. Let's go with visibility: public and permissions: write for the org-level boards. Will update the description.
I have updated https://github.com/kubernetes/community/issues/3280#issuecomment-465492138 to list access options for all org-level project boards. IMO we should go for Public + Write as a default, but not enforce this on all boards.
For example, I don't think everyone should have write access to the API Reviews project board and this should only be scoped to the API reviewers/approvers. cc @liggitt
IIRC this was also a reason why write access to the Contributor Experience project board was limited to only a few folks. cc @cblecker @parispittman
@justaugustus does this sound ok to you from a PM perspective?
For example, I don't think everyone should have write access to the API Reviews project board and this should only be scoped to the API reviewers/approvers. cc @liggitt
correct, the current permissions are desired (read access for public and org members, write access for approvers/reviewers teams)
Given that people have preferences that are more or less restrictive than the proposed defaults, and we can't actually set a default, this sounds like guidelines / docs more than automated enforcement
this sounds like guidelines / docs more than automated enforcement
Created #3300
I think we can close this issue once we make all org-level boards Public.
@mariantalla any objections for making the 1.14 CI Signal board public?
@bowei any objections for making the SIG Network board public?
I can flip the settings from Private to Public if this sgty.
Looks like all the boards are public now. Thanks for working on this and writing up what was discussed here, @nikhita! :)
/close
@justaugustus: Closing this issue.
In response to this:
Looks like all the boards are public now. Thanks for working on this and writing up what was discussed here, @nikhita! :)
/close
Instructions for interacting with me using PR comments are available here. If you have questions or suggestions related to my behavior, please file an issue against the kubernetes/test-infra repository.
SIG Network was still Private but I've flipped it to Public.
Most helpful comment
Given that people have preferences that are more or less restrictive than the proposed defaults, and we can't actually set a default, this sounds like guidelines / docs more than automated enforcement