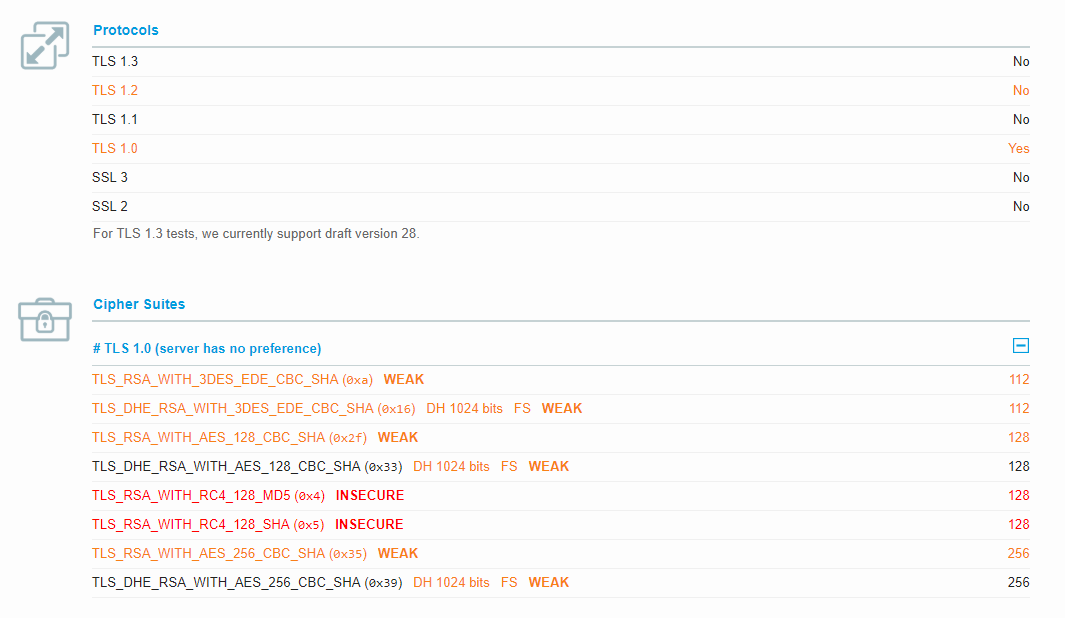
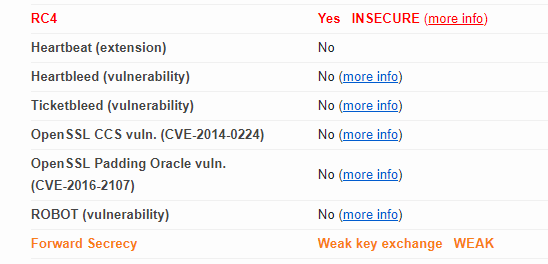
caniuse.com only supports TLS 1.0, unsafe RC4, only supports weak cipher suites
The Can I Use webserver only support TLS 1.0, allows RC4 cipher suites, and only supports extremely weak cipher suites.
TLS 1.0 and even 1.1 are being deprecated at this point, and RC4 cipher suites have been known unsafe for years and the IETF themselves proposed their prohitibition in 2015.
Please at the minimum support TLS 1.2/1.1 and disable RC4 suites.
Recommend only allowing TLS 1.2, and AEAD cipher suites.
All 11 comments
Test: https://www.ssllabs.com/ssltest/analyze.html?d=caniuse.com&hideResults=on
C rating. That's indeed weak.
Any news? Anything we can help? Note that TLS 1.3 has finally made it to RFC 8446.
Still C rating unfortunately (https://www.ssllabs.com/ssltest/analyze.html?d=caniuse.com&hideResults=on)
Summary:

Any update on this? There really is no excuse not to have TLS 1.2 enabled at this point. There is already an IETF draft to disable TLS 1.0. Please enable TLS 1.2.
Four browser engines announced a schedule for removal of TLS 1.0 and 1.1:
https://blog.mozilla.org/security/2018/10/15/removing-old-versions-of-tls/
https://security.googleblog.com/2018/10/modernizing-transport-security.html
https://blogs.windows.com/msedgedev/2018/10/15/modernizing-tls-edge-ie11/
https://webkit.org/blog/8462/deprecation-of-legacy-tls-1-0-and-1-1-versions/
bump @Fyrd
Working on it. Hope to have it updated by the end of the month.
Alright folks, TLS 1.2 supported and an "A+" on SSL Labs now ☺️
Can confirm.
- [x] 4096-bit certificate (default of certbot is 2048-bit)
- [x] 4096-bit Diffie-Hellman (anything equal to or higher than 2048 is good)
- [x] No RSA as key-exchange algorithm, so all ciphers support Perfect Forward Secrecy.
- [x] EDCHE (to save computation for both browser and server)
- [x] No TLS 1.0 (PCI Compliance)
This is outstanding.
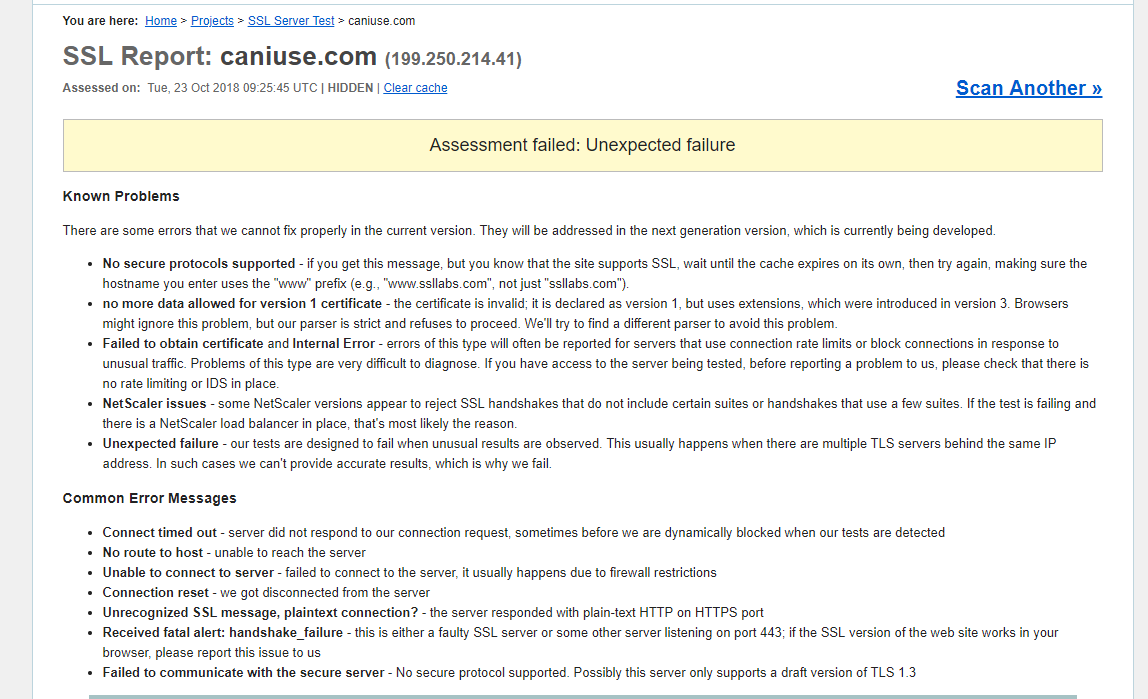
Funny, SSL labs crashes on me. Not sure if this is an issue of SSL labs:
try 1:
try 2:
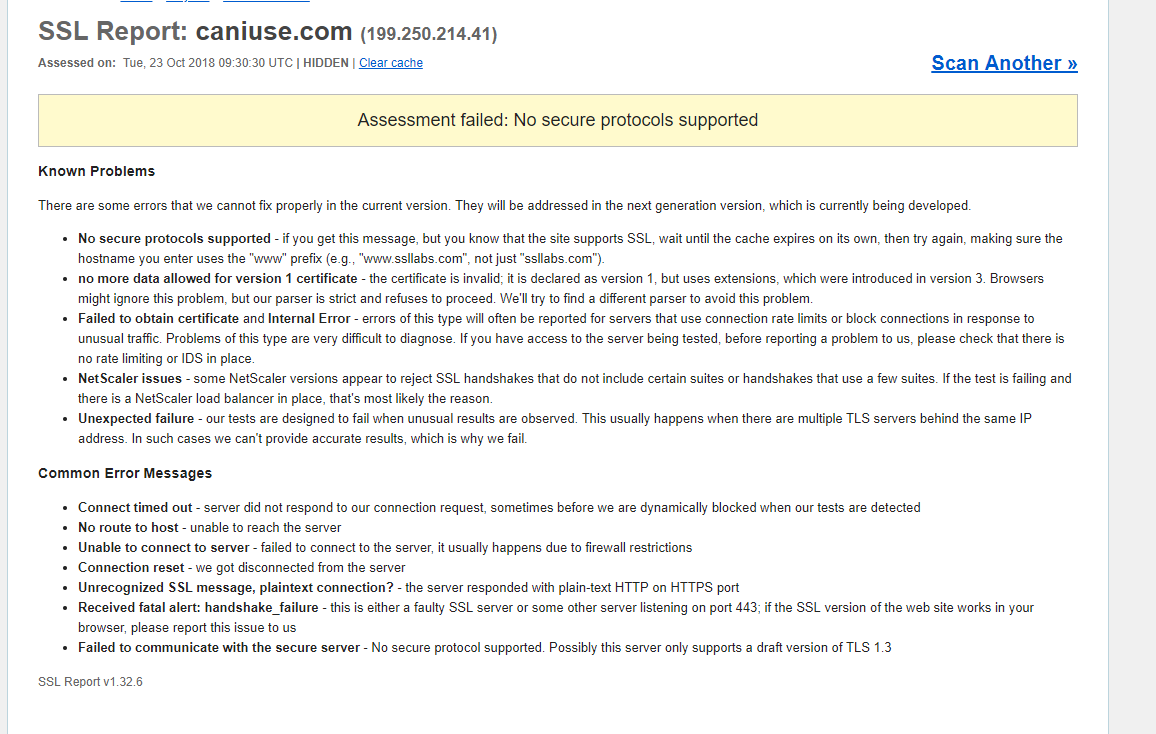
update: caniuse.com is down/unstable.
Most helpful comment
Alright folks, TLS 1.2 supported and an "A+" on SSL Labs now ☺️