Azure-docs: Incorrect RSA and Symmetric Key Size
[Enter feedback here]
Two instances
The example below shows how to create a 3070-bit RSA key that will be only used for wrapKey, unwrapKey operations (--ops).
but the example is for 3072-bit
az keyvault key create --hsm-name ContosoMHSM --name myrsakey --ops wrapKey unwrapKey --kty RSA-HSM --size 3072
also
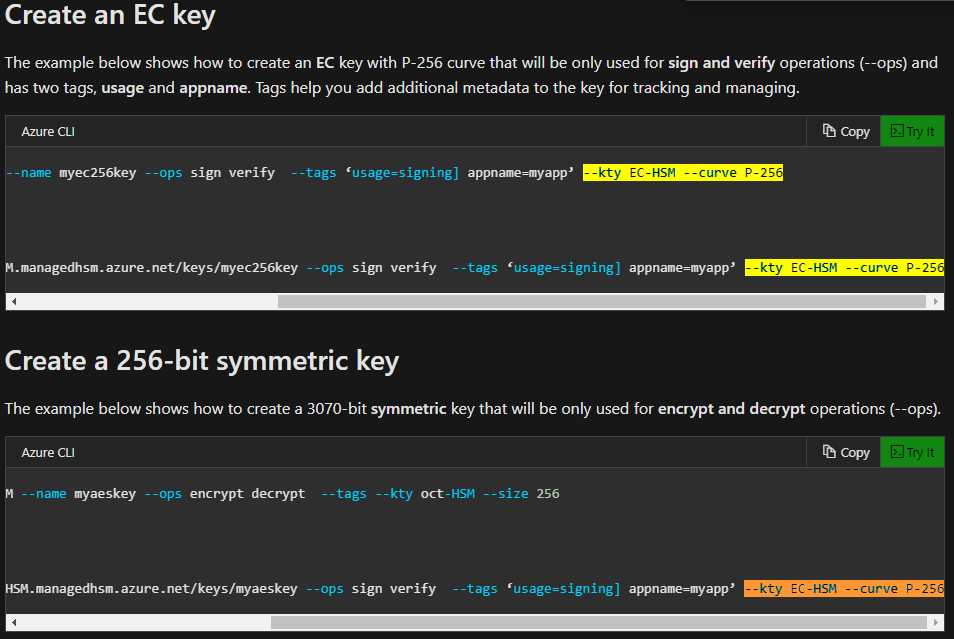
The example below shows how to create a 3070-bit symmetric key that will be only used for encrypt and decrypt operations (--ops).
the example is:
az keyvault key create --hsm-name ContosoMHSM --name myaeskey --ops encrypt decrypt --tags --kty oct-HSM --size 256
Also, the example references EC:
az keyvault key create --id https://ContosoMHSM.managedhsm.azure.net/keys/myaeskey --ops sign verify --tags ‘usage=signing] appname=myapp’ --kty EC-HSM --curve P-256
when it should be AES
Document Details
⚠ Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.
- ID: 73a19fb7-9612-02ba-846f-b42295cbf16f
- Version Independent ID: ac20cc02-dca2-d836-68a5-83d6df8a90f0
- Content: Manage keys in a managed HSM - Azure Key Vault
- Content Source: articles/key-vault/managed-hsm/key-management.md
- Service: key-vault
- Sub-service: managed-hsm
- GitHub Login: @amitbapat
- Microsoft Alias: ambapat
All 7 comments
@x509cert
Thanks for your feedback! We will investigate and update as appropriate.
@x509cert
Thanks for your feedback! I have assigned this issue to the author who will investigate and update as appropriate.
@x509cert
I've created a PR to update the text to reflect the correct keys 3072 and 256.
However, I'll let the author investigate and update the actual code change to AES.
i think the last example is also incorrect, as you're using an AES key and then an EC key - the latter is not a symmetric key. lemme know if you need to chat...
Thanks for pointing out the error on EC key. I have pushed a fix. Should be live soon.
Checking to see if the changes are live and if this request could be archived?
Fixed #please-close