Azure-docs: How to get v2 access token?
Using https://login.microsoftonline.com/{tenantId}/oauth2/v2.0/token to get token but returns v1.0. And app registration manifest "accessTokenAcceptedVersion": 2 but still getting V1.0
"app_displayname": "Gateway_Authentication",
"appid": "29327a53-7dd4-4afd-80dd-ce574de5c1ce",
"ver": "1.0",
What else is missing?
Document Details
⚠ Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.
- ID: 3cd73bb0-f8d5-84f7-3fc5-2022f8392a20
- Version Independent ID: d598130d-ba3a-0078-d4b6-1e47fad5ea41
- Content: Microsoft identity platform and OAuth2.0 On-Behalf-Of flow
- Content Source: articles/active-directory/develop/v2-oauth2-on-behalf-of-flow.md
- Service: active-directory
- Sub-service: develop
- GitHub Login: @rwike77
- Microsoft Alias: ryanwi
All 8 comments
Hi @stalinponnusamy
Kindly link the doc that you are following so that we can better assist you.
Topic : Microsoft identity platform and the OAuth 2.0 client credentials flow
Header : Get a token
Sub Header : First case: Access token request with a shared secret
Link:
https://login.microsoftonline.com/a2c2f5ee-45ac-4f21-93e7-b05ba44d3b25/oauth2/v2.0/authorize?client_id=29327a53-7dd4-4afd-80dd-ce574de5c1ce&redirect_uri=https://snv2app.azurewebsites.net&response_type=id_token+token&scope=openid api://f3d966c0-517e-4e13-a5bb-9777a916b1a0/User.read&response_mode=fragment&nonce=123
Request
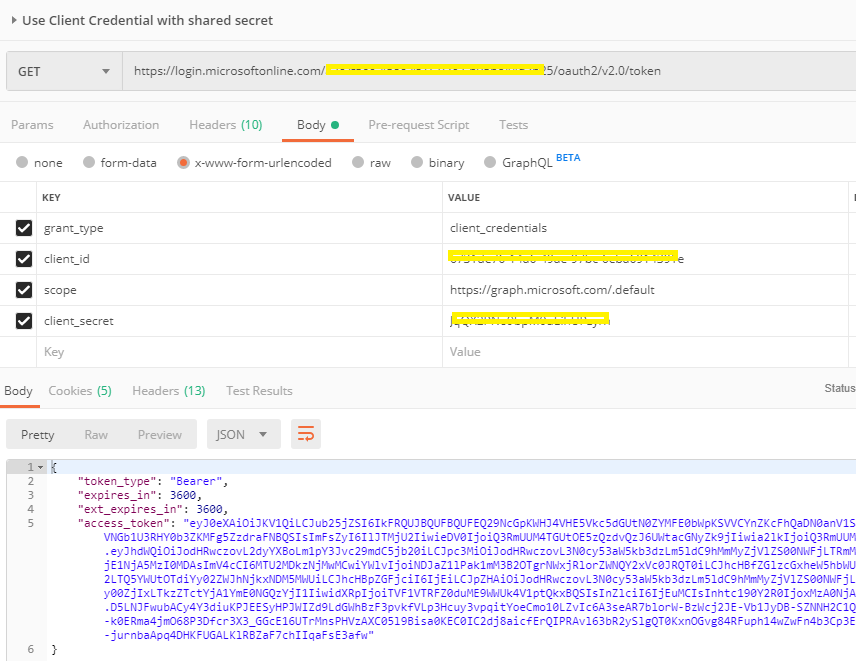
Response Token

Hi @stalinponnusamy
Have you seen this thread below? It looks like it might be related.
You can try creating a new client using https://apps.dev.microsoft.com/ and setting the accessTokenAcceptedVersion:2 in the WebApiApp manifest.
https://stackoverflow.com/questions/54278212/azure-ad-getting-wrong-token-version
Also, check this thread as well. https://github.com/AzureAD/microsoft-authentication-library-for-dotnet/issues/575
Hi Marilee, I refereed but no luck. Architecture plan to use Azure AD as token issuer and authenticate on Layer 7 to consume onprem API.
Azure Function (Get Token) --> Layer 7 (CA Gateway) --> onprem (Exposed API)
Getting V1 token.
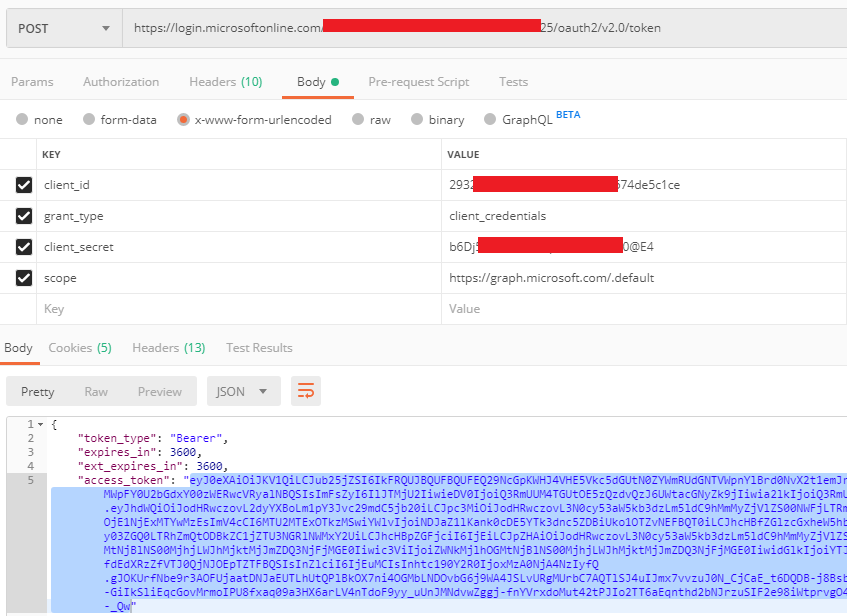
Question : Is it possible to get V2 azure token without specifying resource. Since resource is an onprem API. Please refer the code sample (Postman)
Code Sample
Hi @stalinponnusamy ,
Sorry for the late reply. I'm not certain what could be causing this but I am reaching out to the product team to see if they might be able to help.
In the meantime, if you want a faster response I would suggest opening a thread on MSDN since this is more of a troubleshooting question than a docs issue.
Access tokens are always generated using the token version of the resource (the WebAPI, Graph in this case). Clients can't change the format of the access token - that would break the web API when they try to interpret the token.
To expand on this - you cannot send tokens with an "aud" of Graph to your own gateway. We'll start encrypting tokens someday, and then that token will become gibberish (to you, without the decryption cert ). Please test this by using a resource/scope that you own.
We will now proceed to close this thread. If you have further questions feel free to tag us in the comments and we will gladly continue the discussion.