Adguardhome: IPv6 server not work
Prerequisites
- [*] I am running the latest version
- [*] I checked the documentation and found no answer
- [*] I checked to make sure that this issue has not already been filed
Issue Details
- Version of AdGuard Home server:
v0.100.8 - How did you setup DNS configuration:
tls://dns.google
[/a.z/10.in-addr.arpa/168.192.in-addr.arpa/8.1.1.0.0.8.5.e.0.0.e.0.4.2.ip6.arpa/]192.168.50.2
- Operating system and version:
Description: Ubuntu 18.04.3 LTS
Expected Behavior
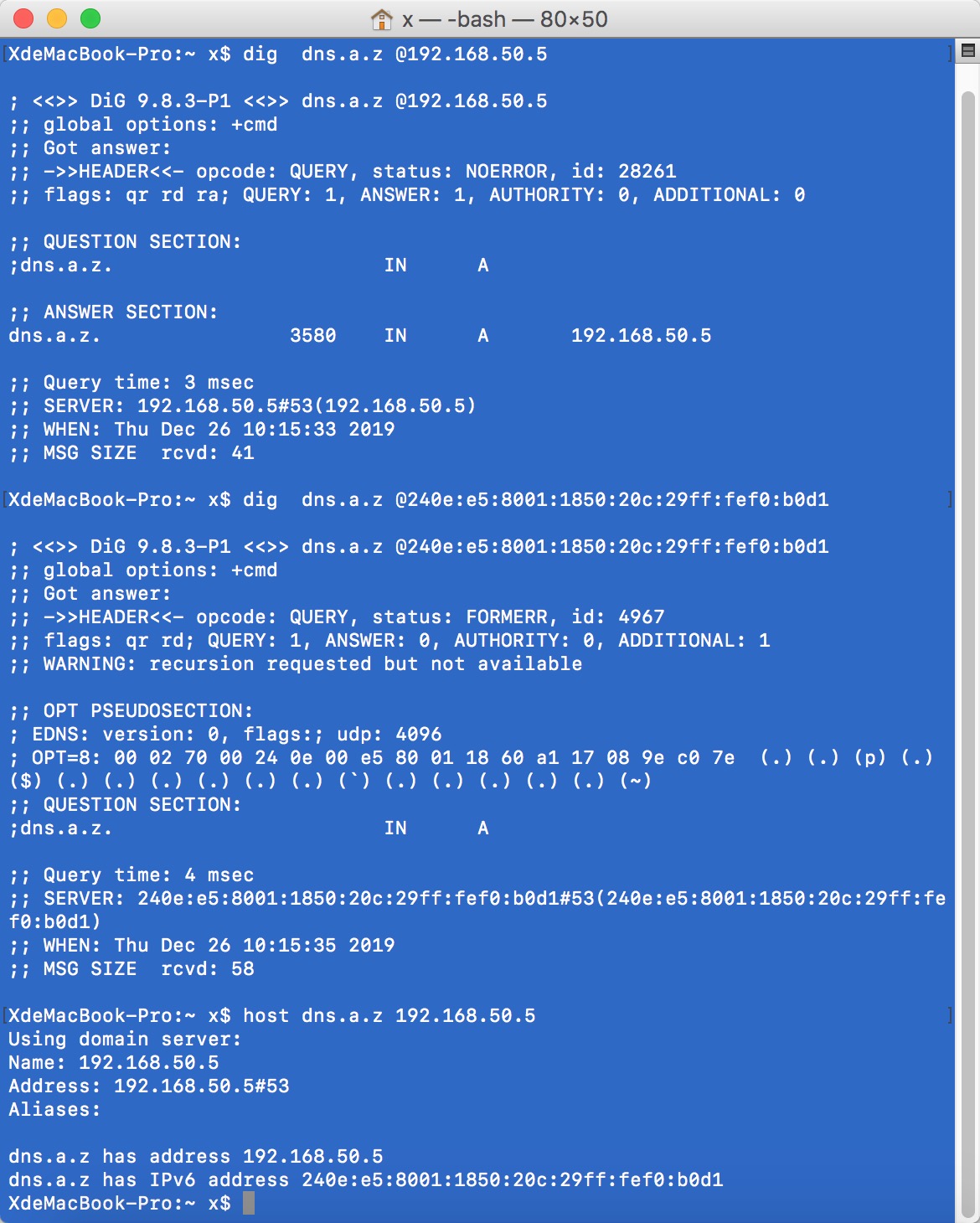
服务器的IPv6与IPv4地址解析结果不同
Actual Behavior
当开启“Enable EDNS Client Subnet”后,通过AdGuard Home DNS server的IPv4地址可以正确解析出私网域名地址,但是AdGuard Home DNS server的IPv6地址是不可以。
Screenshots
Additional Information
All 8 comments
To troubleshoot this issue we need to see AdGuard Home logs.
- Configure AdGuard Home to collect logs:
- Specify
log_file - Set
verbosetoTrue
- Specify
- Restart AdGuard Home and reproduce the issue
- Post the log file here.
Could you please do cat log | grep -A 10 -B 10 52495, this log's missing some context
To troubleshoot this issue we need to see AdGuard Home logs.
Configure AdGuard Home to collect logs:
- Specify
log_file- Set
verbosetoTrue- Restart AdGuard Home and reproduce the issue
- Post the log file here.
cetc50@dns:/opt/AdGuardHome$ cat log | grep -A 10 -B 10 51808
2019/12/26 17:14:39 3972#51798 [debug] github.com/AdguardTeam/AdGuardHome/dnsfilter.(*Dnsfilter).checkSafeBrowsing(): SafeBrowsing lookup for s.yimg.com; Elapsed time: 64ms
2019/12/26 17:14:39 3972#51798 [debug] github.com/AdguardTeam/AdGuardHome/dnsfilter.(*Dnsfilter).checkParental(): Parental: checking s.yimg.com: 9919d06e.46b1adbb.pc.dns.adguard.com.
2019/12/26 17:14:39 3972#51813 [debug] github.com/AdguardTeam/dnsproxy/proxy.(*Proxy).handleUDPPacket(): Start handling new UDP packet from 192.168.50.59:50644
2019/12/26 17:14:39 3972#51813 [debug] github.com/AdguardTeam/dnsproxy/proxy.(*Proxy).logDNSMessage(): IN: ;; opcode: QUERY, status: NOERROR, id: 57960
;; flags: rd; QUERY: 1, ANSWER: 0, AUTHORITY: 0, ADDITIONAL: 0
;; QUESTION SECTION:
;access-prod.apis.anvato.net. IN A
2019/12/26 17:14:39 3972#51813 [debug] github.com/AdguardTeam/AdGuardHome/dnsfilter.(*Dnsfilter).checkSafeBrowsing(): SafeBrowsing: checking access-prod.apis.anvato.net: 6b6fc270.f0396ad0.22e50cd6.sb.dns.adguard.com.
2019/12/26 17:14:39 3972#51808 [debug] github.com/AdguardTeam/dnsproxy/proxy.(*Proxy).handleUDPPacket(): Start handling new UDP packet from [240e:e5:8001:1860:413a:9002:d6af:2d72]:57168
2019/12/26 17:14:39 3972#51808 [debug] github.com/AdguardTeam/dnsproxy/proxy.(*Proxy).logDNSMessage(): IN: ;; opcode: QUERY, status: NOERROR, id: 5919
;; flags: rd; QUERY: 1, ANSWER: 0, AUTHORITY: 0, ADDITIONAL: 0
;; QUESTION SECTION:
;fandi-pc.a.z. IN A
2019/12/26 17:14:39 3972#51808 [debug] github.com/AdguardTeam/AdGuardHome/dnsfilter.(*Dnsfilter).checkSafeBrowsing(): SafeBrowsing: checking fandi-pc.a.z: 984b9fc6.9111cd73.594e519a.sb.dns.adguard.com.
2019/12/26 17:14:39 3972#51795 [debug] github.com/AdguardTeam/AdGuardHome/dnsfilter.(*Dnsfilter).processTXT(): Parental: hashes for static.chinatimes.com: []
2019/12/26 17:14:39 3972#51795 [debug] Parental: stored in cache: static.chinatimes.com (149 bytes)
2019/12/26 17:14:39 3972#51795 [debug] github.com/AdguardTeam/AdGuardHome/dnsfilter.(*Dnsfilter).checkParental(): Parental lookup for static.chinatimes.com; Elapsed time: 62ms
2019/12/26 17:14:39 3972#51818 [debug] github.com/AdguardTeam/dnsproxy/upstream.(*TLSPool).Get(): Returning existing connection to 8.8.4.4:853 with updated deadLine
2019/12/26 17:14:39 3972#51798 [debug] github.com/AdguardTeam/AdGuardHome/dnsfilter.(*Dnsfilter).processTXT(): Parental: hashes for s.yimg.com: []
2019/12/26 17:14:39 3972#51798 [debug] Parental: stored in cache: s.yimg.com (149 bytes)
2019/12/26 17:14:39 3972#51798 [debug] github.com/AdguardTeam/AdGuardHome/dnsfilter.(*Dnsfilter).checkParental(): Parental lookup for s.yimg.com; Elapsed time: 62ms
2019/12/26 17:14:39 3972#51829 [debug] github.com/AdguardTeam/dnsproxy/upstream.(*TLSPool).Get(): Returning existing connection to 8.8.4.4:853 with updated deadLine
2019/12/26 17:14:39 3972#51795 [debug] github.com/AdguardTeam/dnsproxy/proxy.(*Proxy).Resolve(): RTT: 1 ms
2019/12/26 17:14:39 3972#51795 [debug] DNSFwd: Checking record A (104.20.38.141) for static.chinatimes.com.
--
;; ANSWER SECTION:
rq.wh.cmcm.com. 245 IN A 110.43.89.13
2019/12/26 17:14:39 3972#51842 [debug] 1 elements serialized via json in 20.09µs: 0 kB, 234/entry, 20.09µs/entry
2019/12/26 17:14:39 3972#51842 [debug] ok "/opt/AdGuardHome/data/querylog.json": 234 bytes written
2019/12/26 17:14:39 3972#51813 [debug] github.com/AdguardTeam/AdGuardHome/dnsfilter.(*Dnsfilter).processTXT(): SafeBrowsing: hashes for access-prod.apis.anvato.net: []
2019/12/26 17:14:39 3972#51813 [debug] SafeBrowsing: stored in cache: access-prod.apis.anvato.net (149 bytes)
2019/12/26 17:14:39 3972#51813 [debug] github.com/AdguardTeam/AdGuardHome/dnsfilter.(*Dnsfilter).checkSafeBrowsing(): SafeBrowsing lookup for access-prod.apis.anvato.net; Elapsed time: 69ms
2019/12/26 17:14:39 3972#51813 [debug] github.com/AdguardTeam/AdGuardHome/dnsfilter.(*Dnsfilter).checkParental(): Parental: checking access-prod.apis.anvato.net: 6b6fc270.f0396ad0.22e50cd6.pc.dns.adguard.com.
2019/12/26 17:14:39 3972#51808 [debug] github.com/AdguardTeam/AdGuardHome/dnsfilter.(*Dnsfilter).processTXT(): SafeBrowsing: hashes for fandi-pc.a.z: []
2019/12/26 17:14:39 3972#51808 [debug] SafeBrowsing: stored in cache: fandi-pc.a.z (149 bytes)
2019/12/26 17:14:39 3972#51808 [debug] github.com/AdguardTeam/AdGuardHome/dnsfilter.(*Dnsfilter).checkSafeBrowsing(): SafeBrowsing lookup for fandi-pc.a.z; Elapsed time: 66ms
2019/12/26 17:14:39 3972#51808 [debug] github.com/AdguardTeam/AdGuardHome/dnsfilter.(*Dnsfilter).checkParental(): Parental: checking fandi-pc.a.z: 984b9fc6.9111cd73.594e519a.pc.dns.adguard.com.
2019/12/26 17:14:39 3972#51845 [debug] github.com/AdguardTeam/dnsproxy/proxy.(*Proxy).handleUDPPacket(): Start handling new UDP packet from 10.4.7.52:55954
2019/12/26 17:14:39 3972#51845 [debug] github.com/AdguardTeam/dnsproxy/proxy.(*Proxy).logDNSMessage(): IN: ;; opcode: QUERY, status: NOERROR, id: 56656
;; flags: rd; QUERY: 1, ANSWER: 0, AUTHORITY: 0, ADDITIONAL: 0
;; QUESTION SECTION:
;master1.teamviewer.com. IN AAAA
2019/12/26 17:14:39 3972#51845 [debug] github.com/AdguardTeam/AdGuardHome/dnsfilter.(*Dnsfilter).checkSafeBrowsing(): SafeBrowsing: found in cache: master1.teamviewer.com
2019/12/26 17:14:39 3972#51845 [debug] github.com/AdguardTeam/AdGuardHome/dnsfilter.(*Dnsfilter).checkSafeBrowsing(): SafeBrowsing lookup for master1.teamviewer.com; Elapsed time: 0ms
2019/12/26 17:14:39 3972#51845 [debug] github.com/AdguardTeam/AdGuardHome/dnsfilter.(*Dnsfilter).checkParental(): Parental: found in cache: master1.teamviewer.com
--
2019/12/26 17:14:39 3972#51849 [debug] ok "/opt/AdGuardHome/data/querylog.json": 278 bytes written
2019/12/26 17:14:39 3972#51821 [debug] github.com/AdguardTeam/AdGuardHome/dnsfilter.(*Dnsfilter).processTXT(): SafeBrowsing: hashes for dmp.eland-tech.com: []
2019/12/26 17:14:39 3972#51821 [debug] SafeBrowsing: stored in cache: dmp.eland-tech.com (149 bytes)
2019/12/26 17:14:39 3972#51821 [debug] github.com/AdguardTeam/AdGuardHome/dnsfilter.(*Dnsfilter).checkSafeBrowsing(): SafeBrowsing lookup for dmp.eland-tech.com; Elapsed time: 65ms
2019/12/26 17:14:39 3972#51821 [debug] github.com/AdguardTeam/AdGuardHome/dnsfilter.(*Dnsfilter).checkParental(): Parental: checking dmp.eland-tech.com: ad60a76d.88be462e.pc.dns.adguard.com.
2019/12/26 17:14:39 3972#51813 [debug] github.com/AdguardTeam/AdGuardHome/dnsfilter.(*Dnsfilter).processTXT(): Parental: hashes for access-prod.apis.anvato.net: []
2019/12/26 17:14:39 3972#51813 [debug] Parental: stored in cache: access-prod.apis.anvato.net (149 bytes)
2019/12/26 17:14:39 3972#51813 [debug] github.com/AdguardTeam/AdGuardHome/dnsfilter.(*Dnsfilter).checkParental(): Parental lookup for access-prod.apis.anvato.net; Elapsed time: 63ms
2019/12/26 17:14:39 3972#51859 [debug] github.com/AdguardTeam/dnsproxy/upstream.(*TLSPool).Get(): Returning existing connection to 8.8.4.4:853 with updated deadLine
2019/12/26 17:14:39 3972#51813 [debug] github.com/AdguardTeam/dnsproxy/proxy.(*Proxy).Resolve(): RTT: 3 ms
2019/12/26 17:14:39 3972#51808 [debug] github.com/AdguardTeam/AdGuardHome/dnsfilter.(*Dnsfilter).processTXT(): Parental: hashes for fandi-pc.a.z: []
2019/12/26 17:14:39 3972#51808 [debug] Parental: stored in cache: fandi-pc.a.z (149 bytes)
2019/12/26 17:14:39 3972#51808 [debug] github.com/AdguardTeam/AdGuardHome/dnsfilter.(*Dnsfilter).checkParental(): Parental lookup for fandi-pc.a.z; Elapsed time: 66ms
2019/12/26 17:14:39 3972#51808 [debug] Set ECS data: 240e:e5:8001:1860:413a:9002:d6af:0/112
2019/12/26 17:14:39 3972#51813 [debug] DNSFwd: Checking record A (35.190.16.125) for access-prod.apis.anvato.net.
2019/12/26 17:14:39 3972#51813 [debug] github.com/AdguardTeam/dnsproxy/proxy.(*Proxy).logDNSMessage(): OUT: ;; opcode: QUERY, status: NOERROR, id: 57960
;; flags: qr rd ra; QUERY: 1, ANSWER: 1, AUTHORITY: 0, ADDITIONAL: 0
;; QUESTION SECTION:
;access-prod.apis.anvato.net. IN A
;; ANSWER SECTION:
access-prod.apis.anvato.net. 300 IN A 35.190.16.125
2019/12/26 17:14:39 3972#51860 [debug] 1 elements serialized via json in 24.925µs: 0 kB, 278/entry, 24.925µs/entry
2019/12/26 17:14:39 3972#51808 [debug] github.com/AdguardTeam/dnsproxy/upstream.exchange(): upstream [240e:e5:8001:1850:a198:9fe7:1d79:6902]:53 successfully finished exchange of ;fandi-pc.a.z. IN A. Elapsed 0 ms.
2019/12/26 17:14:39 3972#51860 [debug] ok "/opt/AdGuardHome/data/querylog.json": 278 bytes written
2019/12/26 17:14:39 3972#51808 [debug] github.com/AdguardTeam/dnsproxy/proxy.(*Proxy).Resolve(): RTT: 0 ms
2019/12/26 17:14:39 3972#51808 [debug] ECS option in response: 240e:e5:8001:1860:413a:9002:d6af:0/0
2019/12/26 17:14:39 3972#51808 [debug] github.com/AdguardTeam/dnsproxy/proxy.(*Proxy).logDNSMessage(): OUT: ;; opcode: QUERY, status: FORMERR, id: 5919
;; flags: qr rd; QUERY: 1, ANSWER: 0, AUTHORITY: 0, ADDITIONAL: 1
;; QUESTION SECTION:
;fandi-pc.a.z. IN A
;; ADDITIONAL SECTION:
;; OPT PSEUDOSECTION:
; EDNS: version 0; flags: ; udp: 4096
; SUBNET: [240e:e5:8001:1860:413a:9002:d6af:0]/112/0
And 52495 also
cetc50@dns:/opt/AdGuardHome$ cat log | grep -A 10 -B 10 52495
;; flags: qr rd ra; QUERY: 1, ANSWER: 0, AUTHORITY: 1, ADDITIONAL: 0
;; QUESTION SECTION:
;www.mo.amap.com. IN A
;; AUTHORITY SECTION:
amap.com. 392 IN SOA ns3.aliyun.com. hostmaster.alibabadns.com. 2018062819 3600 1200 3600 360
2019/12/26 17:14:44 3972#52494 [debug] 1 elements serialized via json in 23.39µs: 0 kB, 311/entry, 23.39µs/entry
2019/12/26 17:14:44 3972#52494 [debug] ok "/opt/AdGuardHome/data/querylog.json": 311 bytes written
2019/12/26 17:14:44 3972#52495 [debug] github.com/AdguardTeam/dnsproxy/proxy.(*Proxy).handleUDPPacket(): Start handling new UDP packet from 10.0.0.169:60492
2019/12/26 17:14:44 3972#52495 [debug] github.com/AdguardTeam/dnsproxy/proxy.(*Proxy).logDNSMessage(): IN: ;; opcode: QUERY, status: NOERROR, id: 27826
;; flags: rd; QUERY: 1, ANSWER: 0, AUTHORITY: 0, ADDITIONAL: 0
;; QUESTION SECTION:
;fandi-pc.a.z. IN A
2019/12/26 17:14:44 3972#52495 [debug] github.com/AdguardTeam/AdGuardHome/dnsfilter.(*Dnsfilter).checkSafeBrowsing(): SafeBrowsing: found in cache: fandi-pc.a.z
2019/12/26 17:14:44 3972#52495 [debug] github.com/AdguardTeam/AdGuardHome/dnsfilter.(*Dnsfilter).checkSafeBrowsing(): SafeBrowsing lookup for fandi-pc.a.z; Elapsed time: 0ms
2019/12/26 17:14:44 3972#52495 [debug] github.com/AdguardTeam/AdGuardHome/dnsfilter.(*Dnsfilter).checkParental(): Parental: found in cache: fandi-pc.a.z
2019/12/26 17:14:44 3972#52495 [debug] github.com/AdguardTeam/AdGuardHome/dnsfilter.(*Dnsfilter).checkParental(): Parental lookup for fandi-pc.a.z; Elapsed time: 0ms
2019/12/26 17:14:44 3972#52495 [debug] github.com/AdguardTeam/dnsproxy/upstream.exchange(): upstream [240e:e5:8001:1850:a198:9fe7:1d79:6902]:53 successfully finished exchange of ;fandi-pc.a.z. IN A. Elapsed 0 ms.
2019/12/26 17:14:44 3972#52495 [debug] github.com/AdguardTeam/dnsproxy/proxy.(*Proxy).Resolve(): RTT: 0 ms
2019/12/26 17:14:44 3972#52495 [debug] DNSFwd: Checking record A (10.2.11.37) for fandi-pc.a.z.
2019/12/26 17:14:44 3972#52495 [debug] github.com/AdguardTeam/dnsproxy/proxy.(*Proxy).logDNSMessage(): OUT: ;; opcode: QUERY, status: NOERROR, id: 27826
;; flags: qr aa rd ra; QUERY: 1, ANSWER: 1, AUTHORITY: 0, ADDITIONAL: 0
;; QUESTION SECTION:
;fandi-pc.a.z. IN A
;; ANSWER SECTION:
fandi-pc.a.z. 900 IN A 10.2.11.37
2019/12/26 17:14:44 3972#52496 [debug] 1 elements serialized via json in 31.439µs: 0 kB, 261/entry, 31.439µs/entry
2019/12/26 17:14:44 3972#52496 [debug] ok "/opt/AdGuardHome/data/querylog.json": 261 bytes written
--
init-china.itunes-apple.com.akadns.net. 300 IN CNAME init.itunes.apple.com.mwcname.com.
init.itunes.apple.com.mwcname.com. 300 IN A 58.220.73.46
init.itunes.apple.com.mwcname.com. 300 IN A 114.236.140.29
init.itunes.apple.com.mwcname.com. 300 IN A 222.186.145.64
init.itunes.apple.com.mwcname.com. 300 IN A 122.226.47.70
init.itunes.apple.com.mwcname.com. 300 IN A 115.223.26.165
init.itunes.apple.com.mwcname.com. 300 IN A 101.227.97.199
2019/12/26 17:18:52 3972#69118 [debug] 1 elements serialized via json in 23.04µs: 0 kB, 520/entry, 23.04µs/entry
2019/12/26 17:18:52 3972#69118 [debug] ok "/opt/AdGuardHome/data/querylog.json": 520 bytes written
2019/12/26 17:18:52 3972#69124 [debug] github.com/AdguardTeam/dnsproxy/proxy.(*Proxy).handleUDPPacket(): Start handling new UDP packet from 10.0.0.119:52495
2019/12/26 17:18:52 3972#69124 [debug] github.com/AdguardTeam/dnsproxy/proxy.(*Proxy).logDNSMessage(): IN: ;; opcode: QUERY, status: NOERROR, id: 16371
;; flags: rd; QUERY: 1, ANSWER: 0, AUTHORITY: 0, ADDITIONAL: 0
;; QUESTION SECTION:
;www.icloud.com. IN A
2019/12/26 17:18:52 3972#69124 [debug] github.com/AdguardTeam/AdGuardHome/dnsfilter.(*Dnsfilter).checkSafeBrowsing(): SafeBrowsing: found in cache: www.icloud.com
2019/12/26 17:18:52 3972#69124 [debug] github.com/AdguardTeam/AdGuardHome/dnsfilter.(*Dnsfilter).checkSafeBrowsing(): SafeBrowsing lookup for www.icloud.com; Elapsed time: 0ms
2019/12/26 17:18:52 3972#69124 [debug] github.com/AdguardTeam/AdGuardHome/dnsfilter.(*Dnsfilter).checkParental(): Parental: found in cache: www.icloud.com
2019/12/26 17:18:52 3972#69124 [debug] github.com/AdguardTeam/AdGuardHome/dnsfilter.(*Dnsfilter).checkParental(): Parental lookup for www.icloud.com; Elapsed time: 0ms
--
2019/12/26 17:21:22 3972#79532 [debug] 1 elements serialized via json in 40.448µs: 0 kB, 309/entry, 40.448µs/entry
2019/12/26 17:21:22 3972#79532 [debug] ok "/opt/AdGuardHome/data/querylog.json": 309 bytes written
2019/12/26 17:21:22 3972#79533 [debug] github.com/AdguardTeam/dnsproxy/proxy.(*Proxy).handleUDPPacket(): Start handling new UDP packet from 10.0.0.235:52661
2019/12/26 17:21:22 3972#79533 [debug] github.com/AdguardTeam/dnsproxy/proxy.(*Proxy).logDNSMessage(): IN: ;; opcode: QUERY, status: NOERROR, id: 37661
;; flags: rd; QUERY: 1, ANSWER: 0, AUTHORITY: 0, ADDITIONAL: 0
;; QUESTION SECTION:
;forecast.sina.cn. IN A
2019/12/26 17:21:22 3972#79533 [debug] github.com/AdguardTeam/AdGuardHome/dnsfilter.(*Dnsfilter).checkSafeBrowsing(): SafeBrowsing: found in cache: forecast.sina.cn
2019/12/26 17:21:22 3972#79538 [debug] github.com/AdguardTeam/dnsproxy/proxy.(*Proxy).handleUDPPacket(): Start handling new UDP packet from 10.0.0.235:52495
2019/12/26 17:21:22 3972#79533 [debug] github.com/AdguardTeam/AdGuardHome/dnsfilter.(*Dnsfilter).checkSafeBrowsing(): SafeBrowsing lookup for forecast.sina.cn; Elapsed time: 0ms
2019/12/26 17:21:22 3972#79538 [debug] github.com/AdguardTeam/dnsproxy/proxy.(*Proxy).logDNSMessage(): IN: ;; opcode: QUERY, status: NOERROR, id: 38754
;; flags: rd; QUERY: 1, ANSWER: 0, AUTHORITY: 0, ADDITIONAL: 0
;; QUESTION SECTION:
;forecast.sina.cn. IN A
2019/12/26 17:21:22 3972#79533 [debug] github.com/AdguardTeam/AdGuardHome/dnsfilter.(*Dnsfilter).checkParental(): Parental: found in cache: forecast.sina.cn
2019/12/26 17:21:22 3972#79533 [debug] github.com/AdguardTeam/AdGuardHome/dnsfilter.(*Dnsfilter).checkParental(): Parental lookup for forecast.sina.cn; Elapsed time: 0ms
2019/12/26 17:21:22 3972#79536 [debug] github.com/AdguardTeam/dnsproxy/upstream.(*TLSPool).Get(): Returning existing connection to 8.8.4.4:853 with updated deadLine
cetc50@dns:/opt/AdGuardHome$
Interesting, so when ECS is set the DNS server does not return any response right?
Interesting, so when ECS is set the DNS server does not return any response right?
当开启ECS后,只有特定域名(e.g. [a.z])无法从IPv6地址响应任何请求,但其他的常规域名可以正常解析。
...
3972#51808 [debug] github.com/AdguardTeam/dnsproxy/proxy.(*Proxy).logDNSMessage(): OUT: ;; opcode: QUERY, status: FORMERR, id: 5919
;; flags: qr rd; QUERY: 1, ANSWER: 0, AUTHORITY: 0, ADDITIONAL: 1
status: FORMERR
It seems that the server didn't like our query and responded with FORMERR. Maybe the server requires that DNS.OPT.Cookie option must be set by us?
@sh0w1ov3 Can you check if dig +subnet=... works?